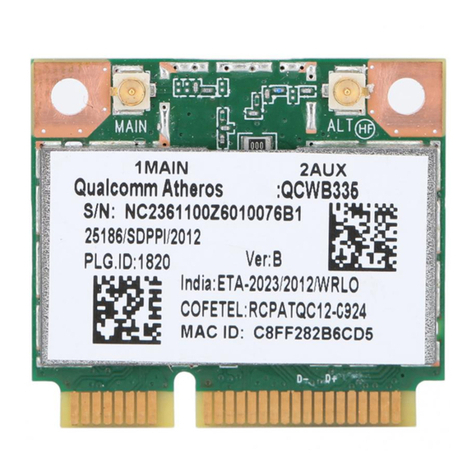
QUALCOMM ATHEROS, INC.
1700 Technology Drive, San Jose, CA 95110
T 408.773.5200 | F 408-773-9940
qca.qualcomm.com
Display Settings .................................................................................................. 22
ACU Tools ........................................................................................................... 22
Tray Icon .............................................................................................................. 23
Color ..................................................................................................................... 24
Quality .................................................................................................................. 24
RSSI* ................................................................................................................... 24
Ad Hoc Mode ...................................................................................................... 24
Ad Hoc Mode Profile Configuration .......................................................... 24
Infrastructure (Access Point) Mode ................................................................... 25
Infrastructure (Access Point) Mode Profile Configuration........................ 25
Uninstall an Old Driver ...................................................................................... 26
Additional Security Features ............................................................................. 26
Message Integrity Check (MIC) ......................................................................... 26
Bluetooth Adapter Installation and Operation ................................................. 27
Getting Started .............................................................................................. 27
Installing the Bluetooth Suite .............................................................................. 27
Downloading the Bluetooth Suite ............................................................... 27
Copying Bluetooth Suite from the CD ........................................................ 28
Launching the Bluetooth Suite ........................................................................... 31
Introduction to the Bluetooth Suite ................................................................... 33
Menu Bar ....................................................................................................... 34
Search For Device................................................................................... 34
Bluetooth Configuration ........................................................................ 34
Bluetooth Help Topics ........................................................................... 35
Bluetooth xchange Folder ................................................................... 35
Bluetooth Places Panel ................................................................................. 35
Uninstalling the Bluetooth Suite ........................................................................ 36
Connecting to an HID Device ............................................................................ 38
Setup Requirements ............................................................................................ 38
Launching the Bluetooth Suite ........................................................................... 38
Connecting to a Sync Device .............................................................................. 41
Setup Requirements ............................................................................................ 41
Launching the Synchronization Process ........................................................... 42
Advanced Status Information ............................................................................ 46
Regulatory Compliance Notices ...........................................................................
USA-Federal Communications Commission (FCC) ............................................
European Community — CE Notice: ....................................................................
Taiwan NCC Radio Compliance: ..........................................................................
2.4GHz Operation ............................................................................................