Linux LINUX ENTERPRISE DESKTOP 10 SP1 - User manual

SUSE Linux Enterprise
www.novell.com10 SP1
May08,2008 The Linux Audit Framework

The Linux Audit Framework
All content is copyright © Novell, Inc.
Legal Notice
This manual is protected under Novell intellectual property rights. By reproducing, duplicating or
distributing this manual you explicitly agree to conform to the terms and conditions of this license
agreement.
This manual may be freely reproduced, duplicated and distributed either as such or as part of a bundled
package in electronic and/or printed format, provided however that the following conditions are ful-
lled:
That this copyright notice and the names of authors and contributors appear clearly and distinctively
on all reproduced, duplicated and distributed copies. That this manual, specically for the printed
format, is reproduced and/or distributed for noncommercial use only. The express authorization of
Novell, Inc must be obtained prior to any other use of any manual or part thereof.
For Novell trademarks, see the Novell Trademark and Service Mark list http://www.novell
.com/company/legal/trademarks/tmlist.html. * Linux is a registered trademark of
Linus Torvalds. All other third party trademarks are the property of their respective owners. A trademark
symbol (®, ™ etc.) denotes a Novell trademark; an asterisk (*) denotes a third party trademark.
All information found in this book has been compiled with utmost attention to detail. However, this
does not guarantee complete accuracy. Neither Novell, Inc., SUSE LINUX Products GmbH, the authors,
nor the translators shall be held liable for possible errors or the consequences thereof.

Contents
About This Guide v
1Understanding Linux Audit 1
1.1 Introducing the Components of Linux Audit . . . . . . . . . . . . . . 3
1.2 Conguring the Audit Daemon . . . . . . . . . . . . . . . . . . . . 5
1.3 Controlling the Audit System Using auditctl . . . . . . . . . . . . . . 10
1.4 Passing Parameters to the Audit System . . . . . . . . . . . . . . . 11
1.5 Understanding the Audit Logs and Generating Reports . . . . . . . . . 15
1.6 Querying the Audit Daemon Logs with ausearch . . . . . . . . . . . . 27
1.7 Analyzing Processes with autrace . . . . . . . . . . . . . . . . . . 31
1.8 Visualizing Audit Data . . . . . . . . . . . . . . . . . . . . . . . 32
2Setting Up the Linux Audit Framework 35
2.1 Determining the Components to Audit . . . . . . . . . . . . . . . 36
2.2 Conguring the Audit Daemon . . . . . . . . . . . . . . . . . . . 37
2.3 Enabling Audit for System Calls . . . . . . . . . . . . . . . . . . . 38
2.4 Setting Up Audit Rules . . . . . . . . . . . . . . . . . . . . . . . 39
2.5 Adjusting the PAM Conguration . . . . . . . . . . . . . . . . . . 40
2.6 Conguring Audit Reports . . . . . . . . . . . . . . . . . . . . . 41
2.7 Conguring Log Visualization . . . . . . . . . . . . . . . . . . . . 44
3Introducing an Audit Rule Set 47
3.1 Adding Basic Audit Conguration Parameters . . . . . . . . . . . . . 48
3.2 Adding Watches on Audit Log Files and Conguration Files . . . . . . . 49
3.3 Monitoring File System Objects . . . . . . . . . . . . . . . . . . . 50
3.4 Monitoring Security Conguration Files and Databases . . . . . . . . . 51
3.5 Monitoring Miscellaneous System Calls . . . . . . . . . . . . . . . . 54

3.6 Filtering System Call Arguments . . . . . . . . . . . . . . . . . . . 54
3.7 Managing Audit Event Records Using Keys . . . . . . . . . . . . . . 57
4Useful Resources 59
ACreating Flow Graphs from the Audit Statistics 61
BCreating Bar Charts from the Audit Statistics 65

About This Guide
The Linux audit framework as shipped with this version of SUSE Linux Enterprise
provides a CAPP-compliant auditing system that reliably collects information about
any security-relevant events. The audit records can be examined to determine whether
any violation of the security policies has been committed and by whom.
Providing an audit framework is an important requirement for a CC-CAPP/EAL certi-
cation. Common Criteria (CC) for Information Technology Security Information is
an international standard for independent security evaluations. Common Criteria helps
customers judge the security level of any IT product they intend to deploy in mission-
critical setups.
Common Criteria security evaluations have two sets of evaluation requirements, func-
tional and assurance requirements. Functional requirements describe the security at-
tributes of the product under evaluation and are summarized under the Controlled Access
Protection Proles (CAPP). Assurance requirements are summarized under the Evalu-
ation Assurance Level (EAL). EAL describes any activities that must take place for the
evaluators to be condent that security attributes are present, effective, and implemented.
Examples for activities of this kind include documenting the developers' search for se-
curity vulnerabilities, the patch process, and testing.
This guide provides a basic understanding of how audit works and how it can be set
up. For more information about Common Criteria itself, refer to the Common Criteria
Web site [http://www.commoncriteria-portal.org].
This guide contains the following:
Understanding Linux Audit
Get to know the different components of the Linux audit framework and how they
interact with each other. Refer to this chapter for detailed background information.
Setting Up the Linux Audit Framework
Follow the instructions to set up an example audit conguration from start to nish.
If you need a quick start document to get you started with audit, this chapter is it.
If you need background information about audit, refer to Chapter 1, Understanding
Linux Audit (page 1) and Chapter 3, Introducing an Audit Rule Set (page 47).

Introducing an Audit Rule Set
Learn how to create an audit rule set that matches your needs by analyzing an ex-
ample rule set.
Useful Resources
Check additional online and system information resources for more details on audit.
1 Feedback
We want to hear your comments and suggestions about this manual and the other doc-
umentation included with this product. Please use the User Comments feature at the
bottom of each page of the online documentation and enter your comments there.
2 Documentation Updates
For the latest version of this documentation, see the SLES 10 SP1 doc Web site
[http://www.novell.com/documentation/sles10].
3 Documentation Conventions
The following typographical conventions are used in this manual:
•/etc/passwd: lenames and directory names
•placeholder: replace placeholder with the actual value
•PATH: the environment variable PATH
•ls,--help: commands, options, and parameters
•user: users or groups
•Alt,Alt +F1: a key to press or a key combination; keys are shown in uppercase as
on a keyboard
•File,File >Save As: menu items, buttons
vi The Linux Audit Framework

•►amd64 ipf: This paragraph is only relevant for the specied architectures. The
arrows mark the beginning and the end of the text block.◄
►ipseries s390 zseries: This paragraph is only relevant for the specied architec-
tures. The arrows mark the beginning and the end of the text block.◄
•Dancing Penguins (Chapter Penguins, ↑Another Manual): This is a reference to a
chapter in another manual.
About This Guide vii


1
Understanding Linux Audit
Linux audit helps make your system more secure by providing you with a means to
analyze what is going on on your system in great detail. It does not, however, provide
additional security itself—it does not protect your system from code malfunctions or
any kind of exploits. Instead, Audit is useful for tracking these issues and helps you
take additional security measures, like Novell AppArmor, to prevent them.
Audit consists of several components, each contributing crucial functionality to the
overall framework. The audit kernel module intercepts the system calls and records the
relevant events. The auditd daemon writes the audit reports to disk. Various command
line utilities take care of displaying, querying, and archiving the audit trail.
Audit enables you to do the following:
Associate Users with Processes
Audit maps processes to the user ID that started them. This makes it possible for
the administrator or security ofcer to exactly trace which user owns which process
and is potentially doing malicious operations on the system.
IMPORTANT: Renaming User IDs
Audit does not handle the renaming of UIDs. Therefore avoid renaming
UIDs (for example, changing tux from uid=1001 to uid=2000) and
obsolete UIDs rather than renaming them. Otherwise you would need to
change auditctl data (audit rules) and would have problems retrieving old
data correctly.
Understanding Linux Audit 1

Review the Audit Trail
Linux audit provides tools that write the audit reports to disk and translate them
into human readable format.
Review Particular Audit Events
Audit provides a utility that allows you to lter the audit reports for certain events
of interest. You can lter for:
• User
• Group
• Audit ID
• Remote Hostname
• Remote Host Address
• System Call
• System Call Arguments
• File
• File Operations
• Success or Failure
Apply a Selective Audit
Audit provides the means to lter the audit reports for events of interest and also
to tune audit to record only selected events. You can create your own set of rules
and have the audit daemon record only those of interest to you.
Guarantee the Availability of the Report Data
Audit reports are owned by root and therefore only removable by root. Unau-
thorized users cannot remove the audit logs.
Prevent Audit Data Loss
If the kernel runs out of memory, the audit daemon's backlog is exceeded, or its
rate limit is exceeded, audit can trigger a shutdown of the system to keep events
from escaping audit's control. This shutdown would be an immediate halt of the
system triggered by the audit kernel component without any syncing of the latest
2The Linux Audit Framework

logs to disk. The default conguration is to log a warning to syslog rather than to
halt the system.
If the system runs out of disk space when logging, the audit system can be cong-
ured to perform clean shutdown (init 0). The default conguration tells the audit
daemon to stop logging when it runs out of disk space.
1.1 Introducing the Components of
Linux Audit
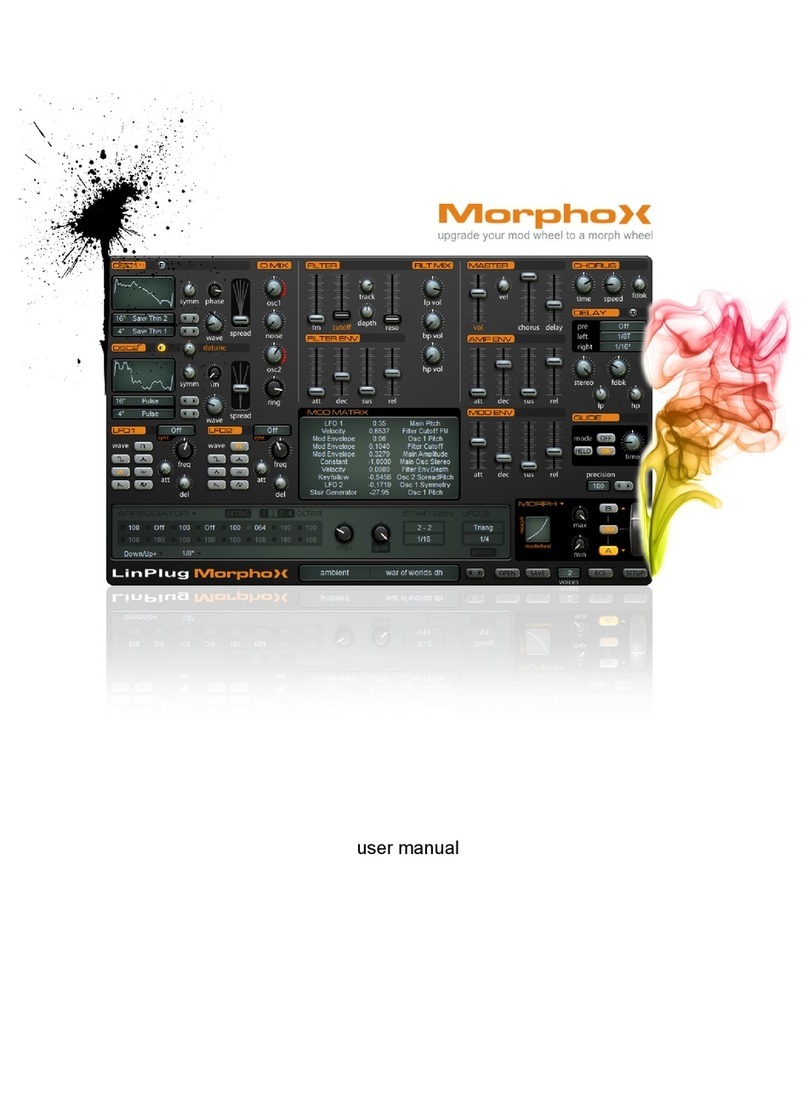
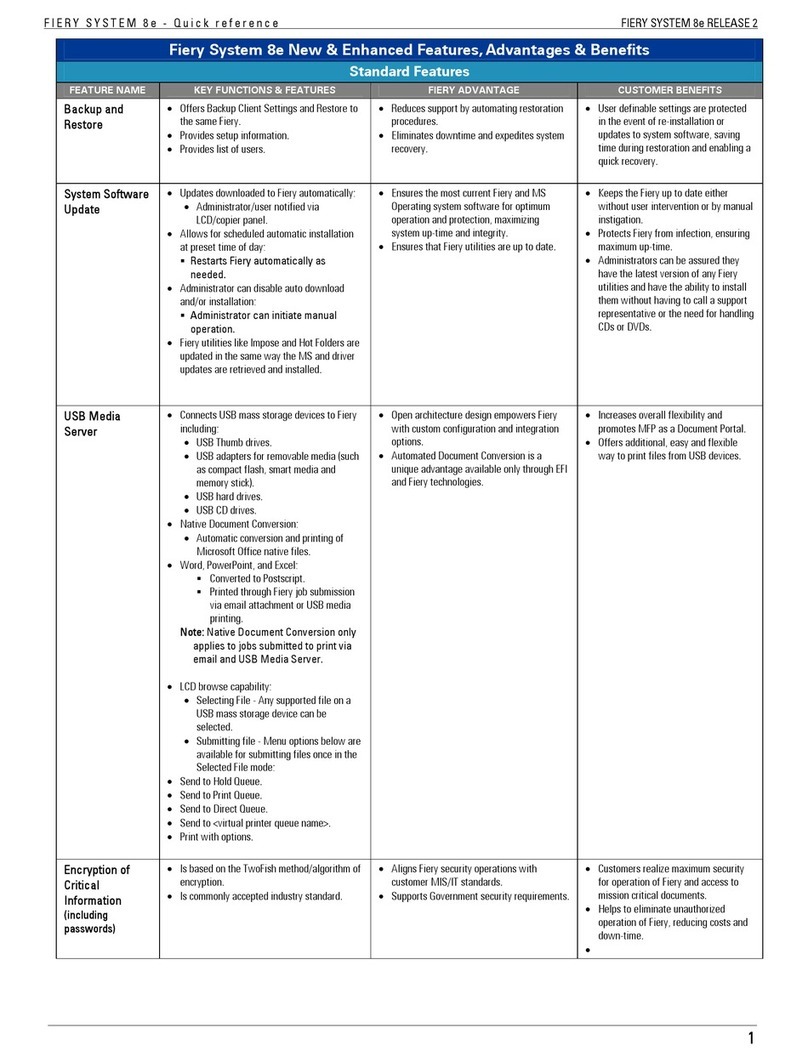
The following gure illustrates how the various components of audit interact with each
other:
Figure 1.1 Introducing the Components of Linux Audit
kernel
audit
auditd
auditd.conf
auditctl
audit.rules
audit.log
audispd
autrace
aureport
ausearch
application
Straight arrows represent the data ow between components while dashed arrows rep-
resent lines of control between components.
auditd
The audit daemon is responsible for writing the audit messages to disk that were
generated through the audit kernel interface and triggered by application and system
activity. How the audit daemon is started is controlled by its conguration le,
Understanding Linux Audit 3

/etc/sysconfig/auditd. How the audit system functions once it is started
is controlled by /etc/auditd.conf. For more information about auditd and
its conguration, refer to Section 1.2, “Conguring the Audit Daemon” (page 5).
auditctl
The auditctl utility controls the audit system. It controls the log generation param-
eters and kernel settings of the audit interface as well as the rule sets that determine
which events are tracked. For more information about auditctl, refer to Section 1.3,
“Controlling the Audit System Using auditctl” (page 10).
audit rules
The le /etc/audit.rules contains a sequence of auditctl commands that
are loaded at system boot time immediately after the audit daemon is started. For
more information about audit rules, refer to Section 1.4, “Passing Parameters to
the Audit System” (page 11).
aureport
The aureport utility allows you to create custom reports from the audit event log.
This report generation can easily be scripted and the output used by various other
applications, for example, to plot these results. For more information about aureport,
refer to Section 1.5, “Understanding the Audit Logs and Generating Reports”
(page 15).
ausearch
The ausearch utility can search the audit log le for certain events using various
keys or other characteristics of the logged format. For more information about
ausearch, refer to Section 1.6, “Querying the Audit Daemon Logs with ausearch”
(page 27).
audispd
The audit dispatcher daemon (audispd) can be used to relay event notications to
other applications instead of or in addition to writing them to disk in the audit log.
autrace
The autrace utility traces individual processes in a fashion similar to strace. The
output of autrace is logged to the audit log. For more information about autrace,
refer to Section 1.7, “Analyzing Processes with autrace” (page 31).
4The Linux Audit Framework

1.2 Conguring the Audit Daemon
Before you can actually start generating audit logs and process them, congure the
audit daemon itself. Congure how it is started in the /etc/sysconfig/auditd
conguration le and congure how the audit system functions once the daemon has
been started in /etc/auditd.conf.
The most important conguration parameters in /etc/sysconfig/auditd are:
AUDITD_LANG="en_US"
AUDITD_DISABLE_CONTEXTS="no"
AUDITD_LANG
The locale information used by audit. The default setting is en_US. Setting it to
none would remove all locale information from audit's environment.
AUDITD_DISABLE_CONTEXTS
Disable system call auditing by default. Set to no for full audit functionality includ-
ing le and directory watches and system call auditing.
The /etc/auditd.conf conguration le determines how the audit system functions
once the daemon has been started. For most use cases, the default settings shipped with
SUSE Linux Enterprise should sufce. For CAPP environments, most of these param-
eters need tweaking. The following list briey introduces the parameters available:
log_file = /var/log/audit/audit.log
log_format = RAW
priority_boost = 3
flush = INCREMENTAL
freq = 20
num_logs = 4
dispatcher = /usr/sbin/audispd
disp_qos = lossy
max_log_file = 5
max_log_file_action = ROTATE
space_left = 75
space_left_action = SYSLOG
action_mail_acct = root
admin_space_left = 50
admin_space_left_action = SUSPEND
disk_full_action = SUSPEND
disk_error_action = SUSPEND
Understanding Linux Audit 5

Depending on whether you want your environment to satisfy the requirements of CAPP,
you need to be extra restrictive when conguring the audit daemon. Where you need
to use particular settings to meet the CAPP requirements, a “CAPP Environment” note
tells you how to adjust the conguration.
log_file and log_format
log_file species the location where the audit logs should be stored.
log_format determines how the audit information is written to disk. Possible
values for log_format are raw (messages are stored just as the kernel sends
them) or nolog (messages are discarded and not written to disk). The data sent
to the audit dispatcher is not affected if you use the nolog mode. The default setting
is raw and you should keep it if you want to be able to create reports and queries
against the audit logs using the aureport and ausearch tools.
NOTE: CAPP Environment
In a CAPP environment, have the audit log reside on its own partition. By
doing so, you can be sure that the space detection of the audit daemon is
accurate and that you do not have other processes consuming this space.
priority_boost
Determine how much of a priority boost the audit daemon should get. Possible
values are 0to 3, with 3assigning the highest priority. The values given here
translate to negative nice values, as in 3to -3 to increase the priority.
flush and freq
Species whether, how, and how often the audit logs should be written to disk.
Valid values for flush are none,incremental,data, and sync.none tells
the audit daemon not to make any special effort to write the audit data to disk.
incremental tells the audit daemon to explicitly ush the data to disk. A fre-
quency must be specied if incremental is used. A freq value of 20 tells the
audit daemon to request the kernel to ush the data to disk after every 20 records.
The data option keeps the data portion of the disk le in sync at all times while
the sync option takes care of both metadata and data.
6The Linux Audit Framework

NOTE: CAPP Environment
In a CAPP environment, make sure that the audit trail is always fully up to
date and complete. Therefore, use sync or data with the flush param-
eter.
num_logs
Specify the number of log les to keep if you have given rotate as the
max_log_file_action. Possible values range from 0to 99. A value less than
2means that the log les are not rotated at all. As you increase the number of les
to rotate, you increase the amount of work required of the audit daemon. While
doing this rotation, auditd cannot always service new data that is arriving from the
kernel as quickly, which can result in a backlog condition (triggering auditd to react
according to the failure ag, described in Section 1.3, “Controlling the Audit System
Using auditctl” (page 10)). In this situation, increasing the backlog limit is recom-
mended. Do so by changing the value of the -b parameter in the /etc/audit
.rules le.
dispatcher and disp_qos
The dispatcher is started by the audit daemon during its start. The audit daemon
relays the audit messages to the application specied in dispatcher. This appli-
cation must be a highly trusted one, because it needs to run as root.disp_qos
determines whether you allow for lossy or lossless communication between
the audit daemon and the dispatcher. If you choose lossy, the audit daemon might
discard some audit messages when the message queue is full. These events still get
written to disk if log_format is set to raw, but they might not get through to
the dispatcher. If you choose lossless the audit logging to disk is blocked until
there is an empty spot in the message queue. The default value is lossy.
max_log_file and max_log_file_action
max_log_file takes a numerical value that species the maximum le size in
megabytes the log le can reach before a congurable action is triggered. The action
to be taken is specied in max_log_file_action. Possible values for
max_log_file_action are ignore,syslog,suspend,rotate, and
keep_logs.ignore tells the audit daemon to do nothing once the size limit is
reached, syslog tells it to issue a warning and send it to syslog, and suspend
causes the audit daemon to stop writing logs to disk leaving the daemon itself still
alive. rotate triggers log rotation using the num_logs setting. keep_logs
Understanding Linux Audit 7

also triggers log rotation, but does not use the num_log setting, so always keeps
all logs.
NOTE: CAPP Environment
To keep a complete audit trail in CAPP environments, the keep_logs
option should be used. If using a separate partition to hold your audit logs,
adjust max_log_file and max_log_file_action to use the entire
space available on that partition.
action_mail_acct
Specify an e-mail address or alias to which any alert messages should be sent. The
default setting is root, but you can enter any local or remote account as long as
e-mail and the network are properly congured on your system and /usr/lib/
sendmail exists.
space_left and space_left_action
space_left takes a numerical value in megabytes of remaining disk space that
triggers a congurable action by the audit daemon. The action is specied in
space_left_action. Possible values for this parameter are ignore,syslog,
email,suspend,single, and halt.ignore tells the audit daemon to ignore
the warning and do nothing, syslog has it issue a warning to syslog, and email
sends an e-mail to the account specied under action_mail_acct.suspend
tells the audit daemon to stop writing to disk but remain alive while single triggers
the system to be brought down to single user mode. halt triggers a full shutdown
of the system.
NOTE: CAPP Environment
Make sure that space_left is set to a value that gives the administrator
enough time to react to the alert and allows him to free enough disk space
for the audit daemon to continue to work. Freeing disk space would involve
calling aureport -t and archiving the oldest logs on a separate archiving
partition or resource. The actual value for space_left depends on the
size of your deployment. Set space_left_action to email.
admin_space_left and admin_space_left_action
admin_space_left takes a numerical value in megabytes of remaining disk
space. The system is already running low on disk space when this limit is reached
8The Linux Audit Framework

and the administrator has one last chance to react to this alert and free disk space
for the audit logs. The value of admin_space_left should be lower than the
value for space_left. The values for admin_space_left_action are the
same as for space_left_action.
NOTE: CAPP Environment
Set admin_space_left to a value that would just allow the administra-
tor's actions to be recorded. The action should be set to single or halt.
disk_full_action
Specify which action to take when the system runs out of disk space for the audit
logs. The possible values are the same as for space_left_action.
NOTE: CAPP Environment
As the disk_full_action is triggered when there is absolutely no more
room for any audit logs, you should bring the system down to single-user
mode (single) or shut it down completely (halt).
disk_error_action
Specify which action to take when the audit daemon encounters any kind of disk
error while writing the logs to disk or rotating the logs. The possible value are the
same as for space_left_action.
NOTE: CAPP Environment
Use syslog,single, or halt depending on your site's policies regarding
the handling of any kind of hardware failure.
Once the daemon conguration in /etc/sysconfig/auditd and /etc/auditd
.conf is complete, the next step is to focus on controlling the amount of auditing the
daemon does and to assign sufcient resources and limits to the daemon so it can operate
smoothly.
Understanding Linux Audit 9

1.3 Controlling the Audit System
Using auditctl
auditctl is responsible for controlling the status and some basic system parameters of
the audit daemon. It controls the amount of auditing performed on the system. Using
audit rules, auditctl controls which components of your system are subjected to the
audit and to what extent they are audited. Audit rules can be passed to the audit daemon
on the auditctl command line as well as by composing a rule set and instructing
the audit daemon to process this le. By default, the rcaudit script is congured to
check for audit rules under /etc/audit.rules. For more details on audit rules,
refer to Section 1.4, “Passing Parameters to the Audit System” (page 11).
The main auditctl commands to control basic audit system parameters are:
•auditctl -e to enable or disable audit
•auditctl -f to control the failure ag
•auditctl -r to control the rate limit for audit messages
•auditctl -b to control the backlog limit
•auditctl -s to query the current status of the audit daemon
The -e,-f,-r, and -b options can also be specied in the audit.rules le to
avoid having to enter them each time the audit daemon is started.
Audit status messages include information on each of the above-mentioned parameters.
The following example highlights the typical audit status message. This message is
output to the terminal any time you query the status of the audit daemon with auditctl
-s or change the status ag with auditctl -e flag.
Example 1.1 Querying the audit Status
AUDIT_STATUS: enabled=1 flag=2 pid=3105 rate_limit=0 backlog_limit=8192 lost=0
backlog=0
10 The Linux Audit Framework

Table 1.1 Audit Status Flags
CommandMeaning [Possible Values]Flag
auditctl -e
[0|1]
Set the enable ag. [0|1]enabled
auditctl -f
[0|1|2]
Set the failure ag. [0..2] 0=silent,
1=printk, 2=panic (immediate halt without
syncing pending data to disk)
flag
—Process ID under which auditd is running.pid
auditctl -r
rate
Set a limit in messages per second. If the
rate is not zero and it is exceeded, the ac-
tion specied in the failure ag is trig-
gered.
rate_limit
auditctl -b
backlog
Specify the maximum number of outstand-
ing audit buffers allowed. If all buffers are
full, the action specied in the failure ag
is triggered.
backlog_limit
—Count the current number of lost audit
messages.
lost
—Count the current number of outstanding
audit buffers.
backlog
1.4 Passing Parameters to the Audit
System
Commands to control the audit system can be invoked individually from the shell using
auditctl or batch read from a le using auditctl -R. This second method is used
by the init scripts to load rules from the le /etc/audit.rules after the audit
daemon has been started. The rules are executed in order from top to bottom. Each of
Understanding Linux Audit 11

these rules would expand to a separate auditctl command. The syntax used in the rules
le is the same as that used for the auditctl command.
Changes made to the running audit system by executing auditctl on the command line
are not persistent across system restarts. For changes to persist, add them to the /etc/
audit.rules le and, if they are not currently loaded into audit, restart the audit
system to load the modied rule set by using the rcauditd restart command.
Example 1.2 Example Audit Rules—Audit System Parameters
-b 1000❶
-f 1❷
-r 10❸
-e 1❹
❶Specify the maximum number of outstanding audit buffers. Depending on the
level of logging activity, you might need to adjust the number of buffers to avoid
causing too heavy an audit load on your system.
❷Specify the failure ag to use. See Table 1.1, “Audit Status Flags” (page 11) for
possible values.
❸Specify the maximum number of messages per second that may be issued by the
kernel. See Table 1.1, “Audit Status Flags” (page 11) for details.
❹Enable or disable the audit subsystem.
Using audit, you can track any kind of le system access to important les, congura-
tions or resources. You can add watches on these and assign keys to each kind of watch
for better identication in the logs.
12 The Linux Audit Framework
Other manuals for LINUX ENTERPRISE DESKTOP 10 SP1 -
1
Table of contents
Other Linux Software manuals
Popular Software manuals by other brands
VMware
VMware THINAPP 4.6 - MIGRATING APPLICATIONS TECHNICAL... Applications
Cabletron Systems
Cabletron Systems SmartSwitch 9A100 Upgrade instructions
Aiphone
Aiphone IS-SOFT Setting manual
Serious Magic
Serious Magic DV RACK manual

Lenovo
Lenovo ThinkServer RD330 Software user's guide

Kyocera
Kyocera Kyocera Extended Driver user guide