8Patch Release Note
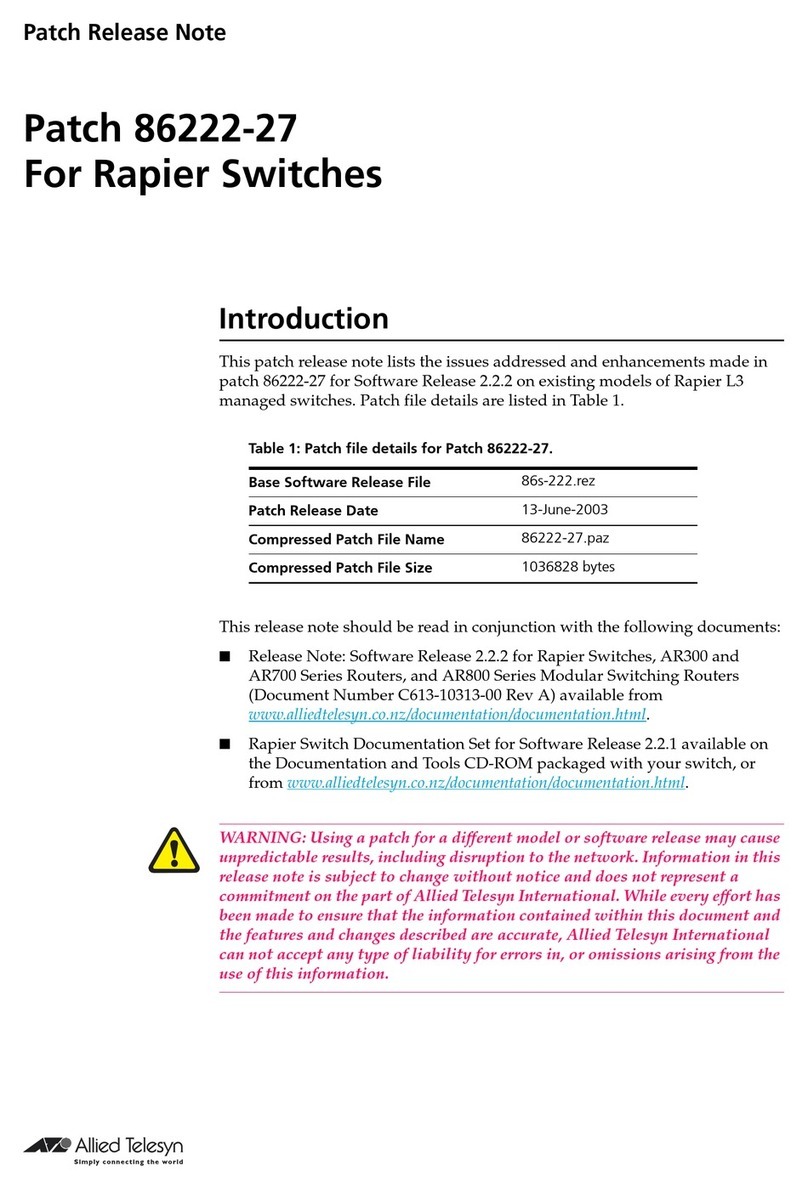
Patch 86222-21 for Software Release 2.2.2
C613-10319-00 REV T
STP always transmits untagged packets. If a port does not belong to a
VLAN as an untagged port, then the port must belong to one VLAN as a
tagged port. In this case, STP should transmit VLAN tagged packets out of
the port.
The IP, MASK, and ACTION parameters could not be set with the SET IP
ROUTE FILTER command. This issue is resolved when the filter number is
specified at the start of the command, for example:
SET IP ROUTE FILTER=filter-id IP=ipadd MASK=ipadd
ACTION={INCLUDE|EXCLUDE}
where: filter-id is the filter number. Filter numbers are displayed in the
output of the SHOW IP ROUTE FILTER command.
The built in Self Test Code for all Rapiers, except G6, has been improved to
enhance the detection of faults in switch chip external packet memory.
An AS boundary router advertises AS external LSAs to other routers.
However, when the router’s configuration changed, either by adding an IP
route filter, or by setting its ASEXTERNAL parameter to OFF using the SET
OSPF ASEXTERNAL command followed by a restart, its neighbour state
could not reach full state. Also, when the router had IP route filters
configured, matched routes were not being flooded into other routers.
However, these routes should still have been imported into the router’s
own LSA database, but were not. These issues have been resolved.
The IPG module has been enhanced to support gratiutous ARP request and
ARP reply packets.
The Rapier was not detecting invalid checksums in ICMP echo request
packets. This issue has been resolved. ICMP echo request packets with
invalid checksums are now dropped and the ICMP inErrors and inDiscards
counters are incremented.
A simple DHCP range MIB and a trap have been added. The trap is
triggered when a DHCP request cannot be satisfied. The gateway address
and the interface address are sent as trap variables. The range table shows
which range was exhausted. A debug variable,
swiDebugBroadcomParityErrors has been added to the SWI module MIB to
count the SDRAM parity errors in the packet memory of the Broadcom
switch chip.
Packets traversing in and out of the same public firewall interface were
sometimes blocked. The firewall should only control packets passing
between a public and a private interface. This issue has been resolved.
PCR: 02098 Module: STP Network affecting: No
PCR: 02123 Module: IPG Network affecting: No
PCR 02138 Module: SWI Network affecting: No
PCR 02140 Module: OSPF Network affecting: No
PCR 02144 Module: IPG Network affecting:No
PCR 02151 Module: IPG Network affecting: No
PCR 02164 Module: DHCP Network affecting: No
PCR 02176 Module: FIREWALL Network affecting: No