User Manual v1.0
www.shield.com 1
Table of Contents
1. Introduction ..........................................................................................................1
1.1. Overview: .................................................................................................................... 1
1.2. STM Deployment Considerations................................................................................ 3
2. Initial Setup & Configuration...............................................................................4
2.2. Default Configuration................................................................................................... 4
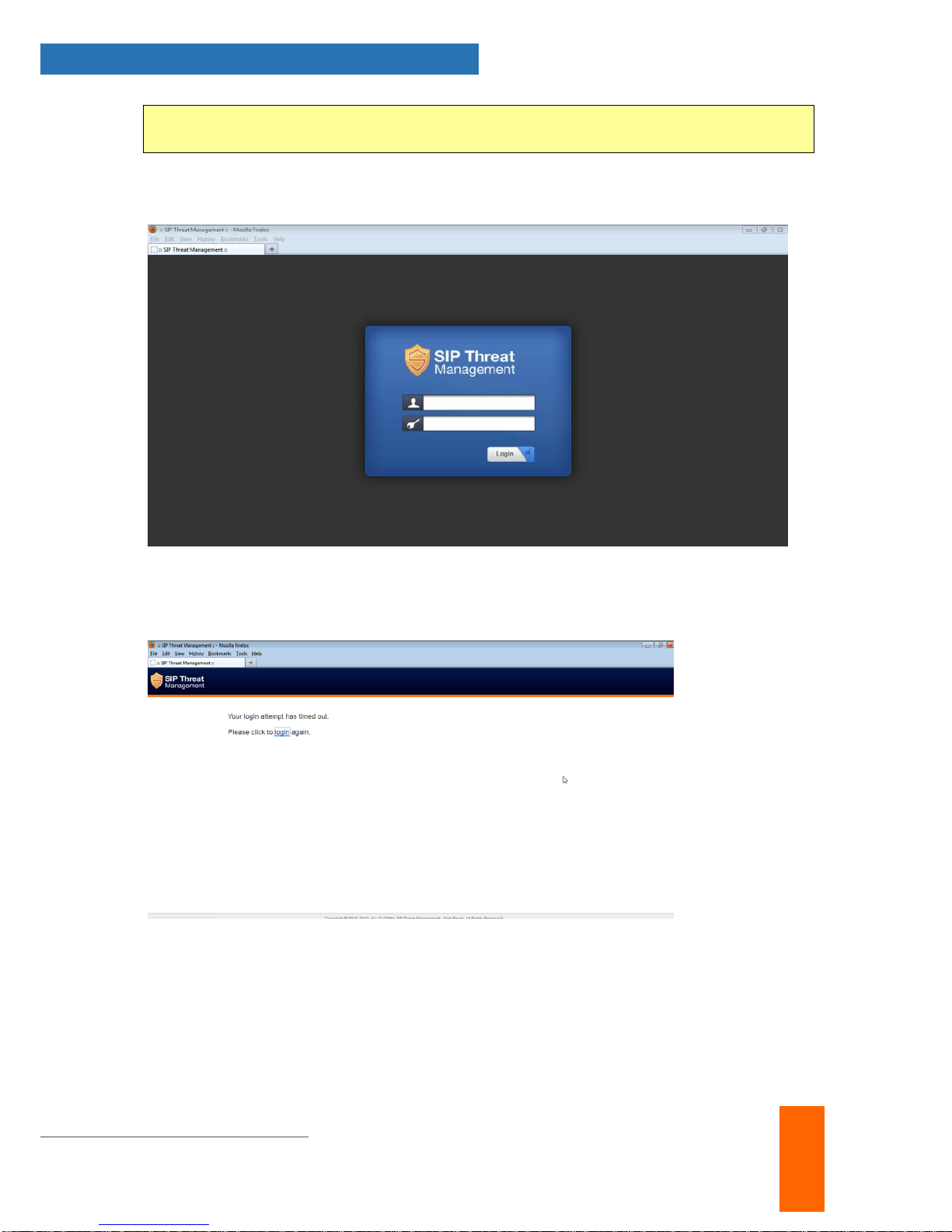
2.3. Accessing the WebUI.................................................................................................. 5
2.4 WebUI Session timeout................................................................................................ 7
2.5 WebUI Settings ............................................................................................................7
2.4 Dashboard.................................................................................................................... 8
3. Configuring the Device........................................................................................9
3.1. General Settings........................................................................................................ 10
3.2. Time Settings ............................................................................................................11
3.3. Management Access................................................................................................. 11
3.4. Signature Update ...................................................................................................... 12
3.5. Logging...................................................................................................................... 13
4. Configuring the SIP Security Policies..............................................................14
4.1. SIP Security Settings................................................................................................. 14
4.2. DPI Signatures.......................................................................................................... 14
4.3. Firewall Rules............................................................................................................ 16
4.4. White list Rules.......................................................................................................... 16
4.5. Blacklist Rules (Static)............................................................................................... 17
4.6. Dynamic Blacklist Rules............................................................................................ 18
4.7. Geo IP Filter.............................................................................................................. 18
5. Status..................................................................................................................19
5.1. Security Alerts........................................................................................................... 19
6. Device Administration .......................................................................................20
6.1. Administration............................................................................................................ 20
6.2. Diagnostics................................................................................................................ 20
6.3. Ping........................................................................................................................... 21