Congratulations!
You have nished conguring the basic settings. Your network is now protected from Internet-
based threats. To explore the full range of conguration options, see the online help or the
Tools and Documentation CD.
Visit these links for more information and documentation for your Fortinet product.
• Technical Documentation - http://docs.forticare.com
• Fortinet Knowledge Center - http://kc.forticare.com
• Fortinet Technical Support - http://support.fortinet.com
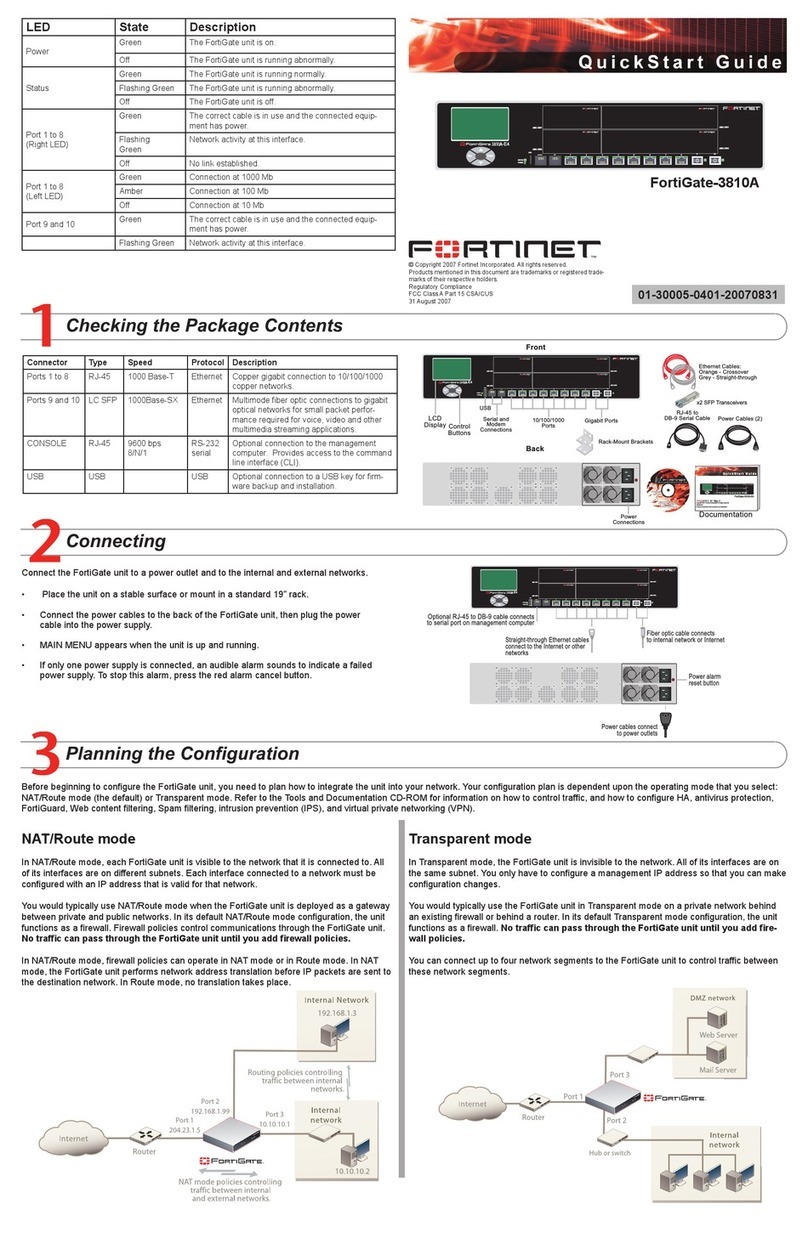
NAT/Route Mode
MGMT 1 IP: ____.____.____.____ Port 8 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
MGMT 2 IP: ____.____.____.____ Port 9 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 1 IP: ____.____.____.____ Port 10 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 2 IP: ____.____.____.____ Port 11 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 3 IP: ____.____.____.____ Port 12 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 4 IP: ____.____.____.____ Port 13 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 5 IP: ____.____.____.____ Port 14 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 6 IP: ____.____.____.____ Port 15 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Port 7 IP: ____.____.____.____ Port 16 IP: ____.____.____.____
Netmask: ____.____.____.____ Netmask: ____.____.____.____
Transparent mode
Management IP IP: ____.____.____.____
Netmask: ____.____.____.____
General settings
Administrator password
Network Settings Default Gateway: ____.____.____.____
Primary DNS Server: ____.____.____.____
Secondary DNS Server: ____.____.____.____
A default gateway is required for the FortiGate unit to route connections to the Internet.
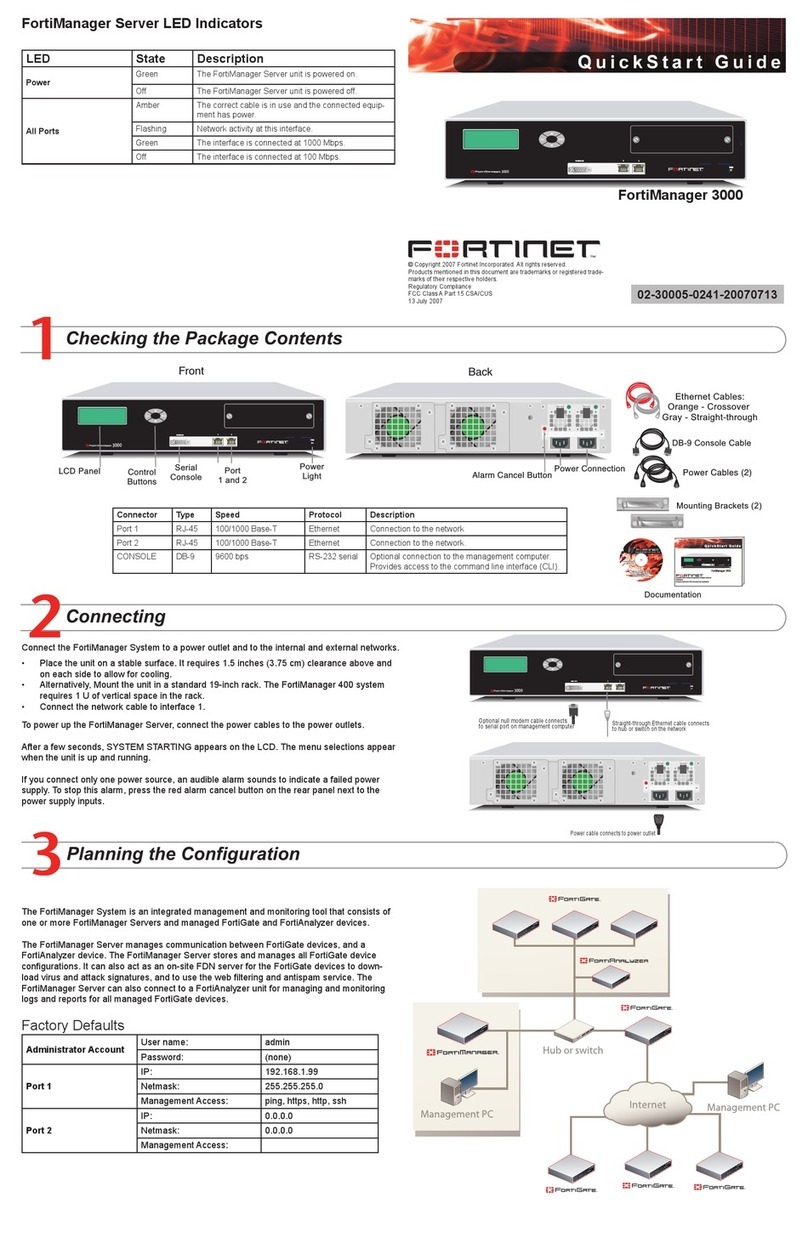
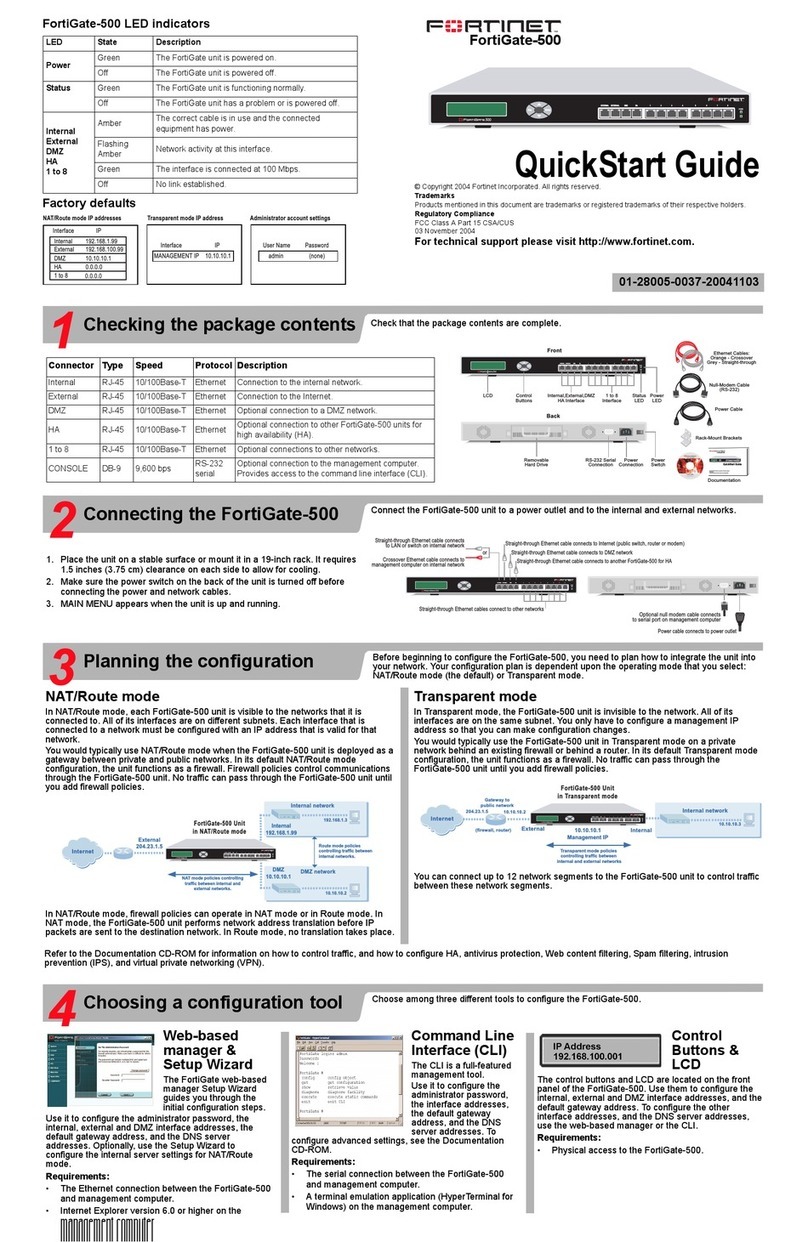
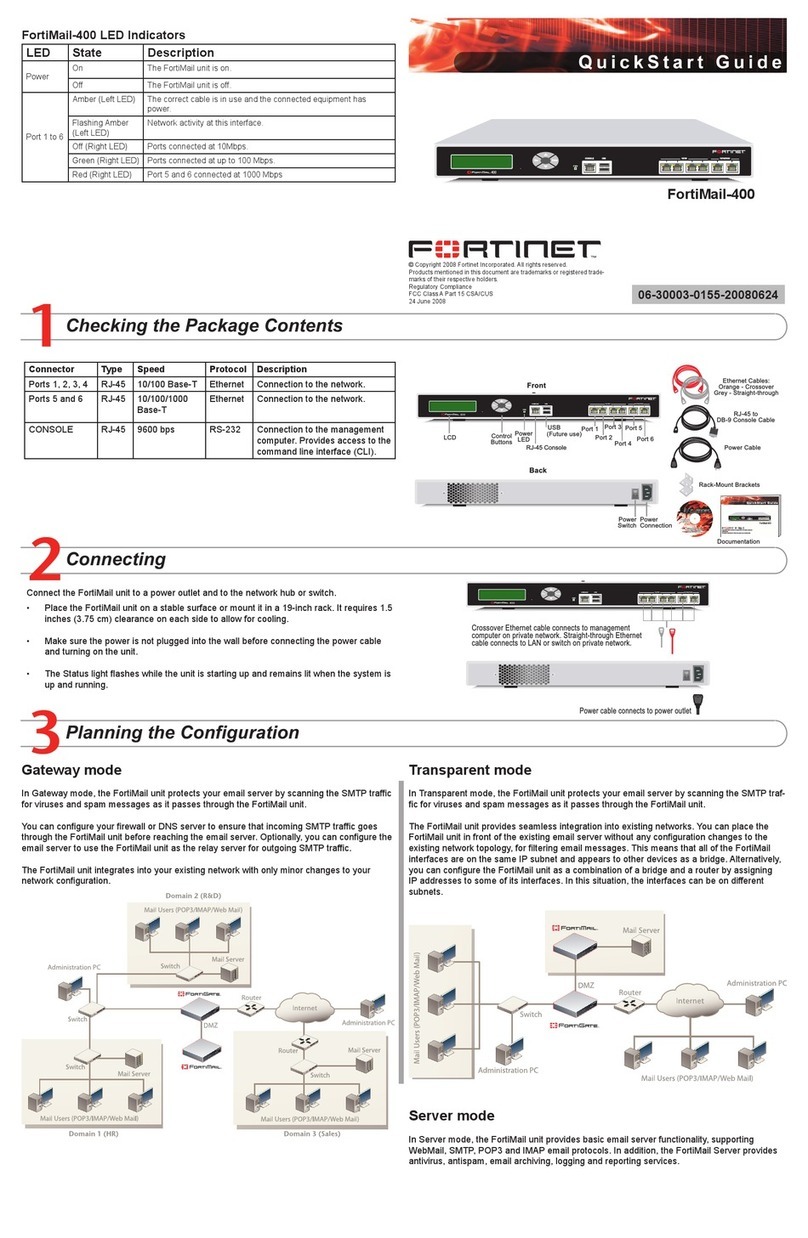
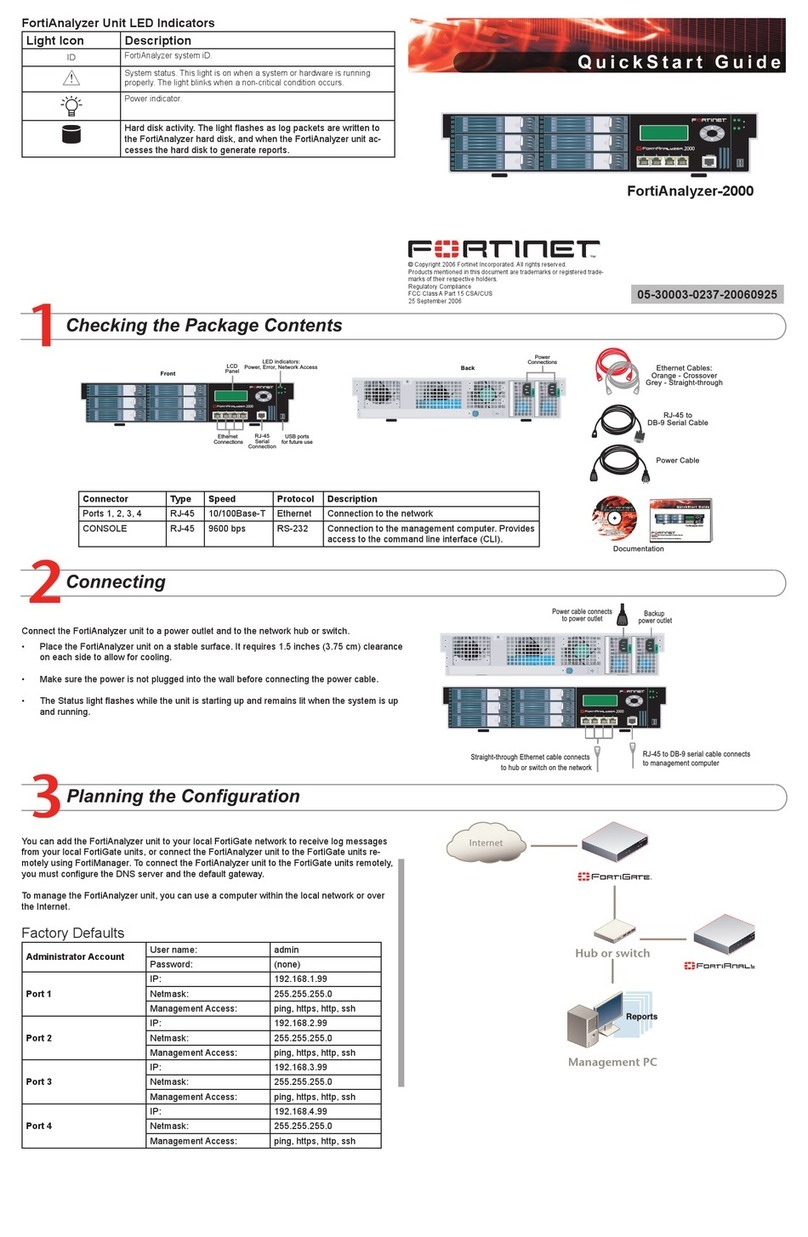
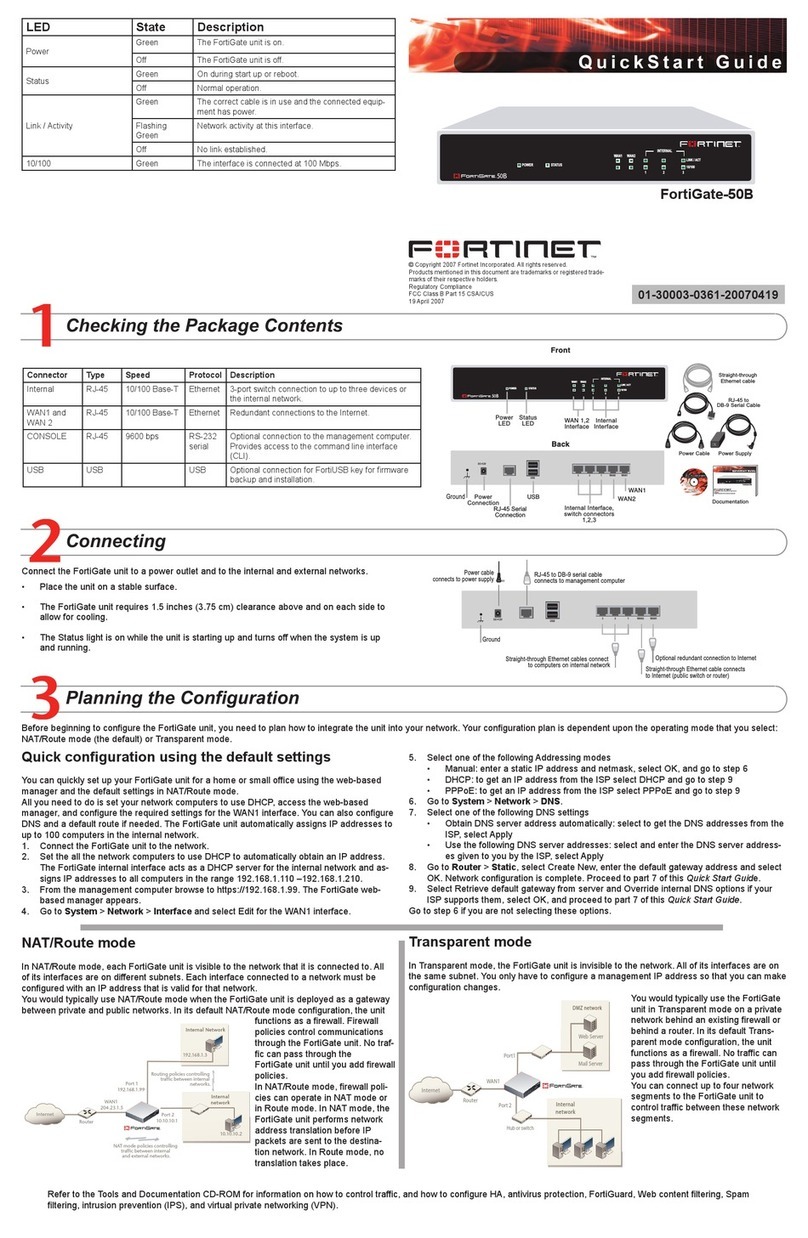
Factory default settings
NAT/Route mode Transparent mode
MGMT 1 192.168.1.99 Management IP 0.0.0.0
MGMT 2 192.168.100.99 Administrative account settings
Ports 1 to 16 0.0.0.0 User name admin
Password (none)
DHCP server on Internal
interface
192.168.1.110 – 192.168.1.210
Web-based Manager
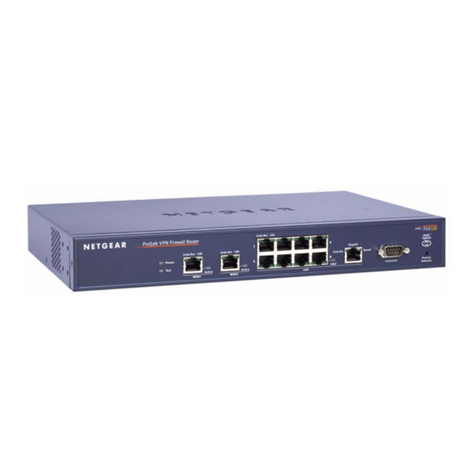
1. Connect the FortiGate internal interface to a management computer Ethernet interface.
Use a cross-over Ethernet cable to connect the devices directly. Use straight-through
Ethernet cables to connect the devices through a hub or switch.
2. Congure the management computer to be on the same subnet as the internal
interface of the FortiGate unit. To do this, change the IP address of the management
computer to 192.168.1.2 and the netmask to 255.255.255.0.
3. To access the FortiGate web-based manager, start Internet Explorer and browse to
https://192.168.1.99 (remember to include the “s” in https://).
4. Type admin in the Name eld and select Login.
NAT/Route mode
To change the administrator password
1. Go to System > Admin > Administrators.
2. Select Change Password for the admin administrator and enter a new password.
To congure interfaces
1. Go to System > Network > Interface.
2. Select the edit icon for each interface to congure.
3. Set the addressing mode for the interface. (See the online help for information.)
• For manual addressing, enter the IP address and netmask for the interface.
• For DHCP addressing, select DHCP and any required settings.
• For PPPoE addressing, select PPPoE, and enter the username and password
and any other required settings.
To congure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > Options, enter the Primary and Secondary DNS IP ad-
dresses that you recorded above and select Apply.
To congure a Default Gateway
1. Go to Router > Static and select Edit icon for the static route.
2. Set Gateway to the Default Gateway IP address you recorded above and select OK.
Transparent mode
To switch from NAT/route mode to transparent mode
1. Go to System > Cong > Operation Mode and select Transparent.
2. Set the Management IP/Netmask to 192.168.1.99/24.
3. Set a default Gateway and select Apply.
To change the administrator password
1. Go to System > Admin > Administrators.
2. Select Change Password for the admin administrator and enter a new password.
To change the management interface
1. Go to System > Cong > Operation Mode.
2. Enter the Management IP address and netmask that you recorded above and select
Apply.
To congure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > Options, enter the Primary and Secondary DNS IP ad-
dresses that you recorded above and select Apply.
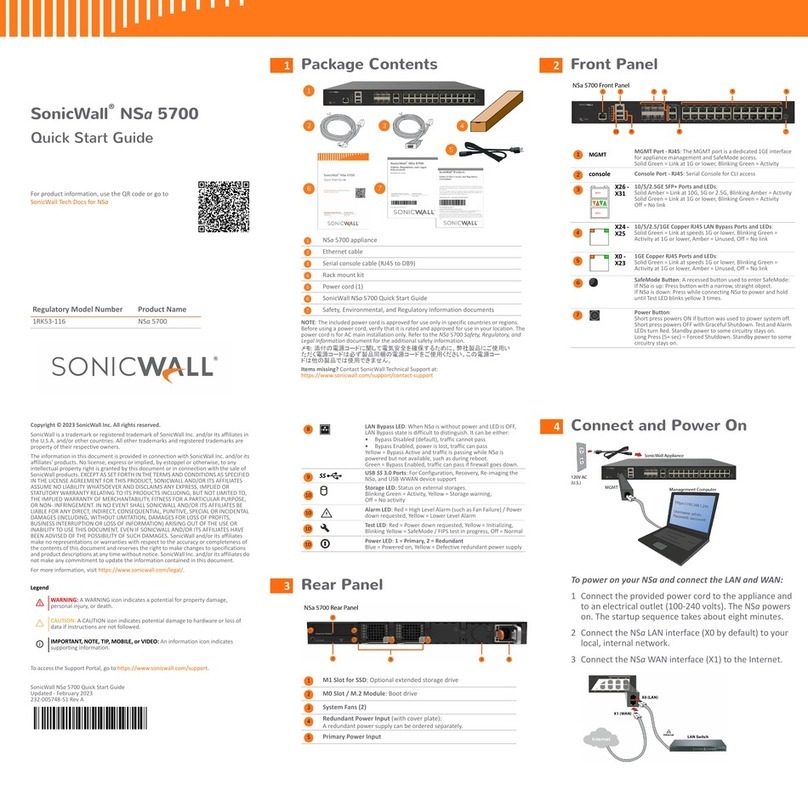
Command Line Interface
1. Use the RJ-45 to DB9 serial cable to connect the FortiGate Console port to the man-
agement computer serial port.
2. Start a terminal emulation program (HyperTerminal) on the management computer. Use
these settings:
3. Baud Rate (bps) 9600, Data bits 8, Parity None, Stop bits 1, and Flow Control None.
4. At the Login: prompt, type admin and press Enter twice (no password required).
NAT/Route mode
1. Congure the FortiGate internal interface.
cong system interface
edit <port_num>
set ip <intf_ip>/<netmask_ip>
set allowaccess {http|https|ssh|ping|snmp|telnet}
end
2. Congure the primary and secondary DNS server IP addresses.
cong system dns
set primary <dns-server_ip>
set secondary <dns-server_ip>
end
3. Congure the default gateway.
cong router static
edit 1
set gateway <gateway_ip>
end
Transparent Mode
1. Change from NAT/Route mode to Transparent mode and congure the Management IP
address.
cong system settings
set opmode transparent
set manageip <mng_ip>/<netmask>
set gateway <gateway_ip>
end
2. Congure the DNS server IP address.
cong system dns
set primary <dns-server_ip>
set secondary <dns-server_ip>
end
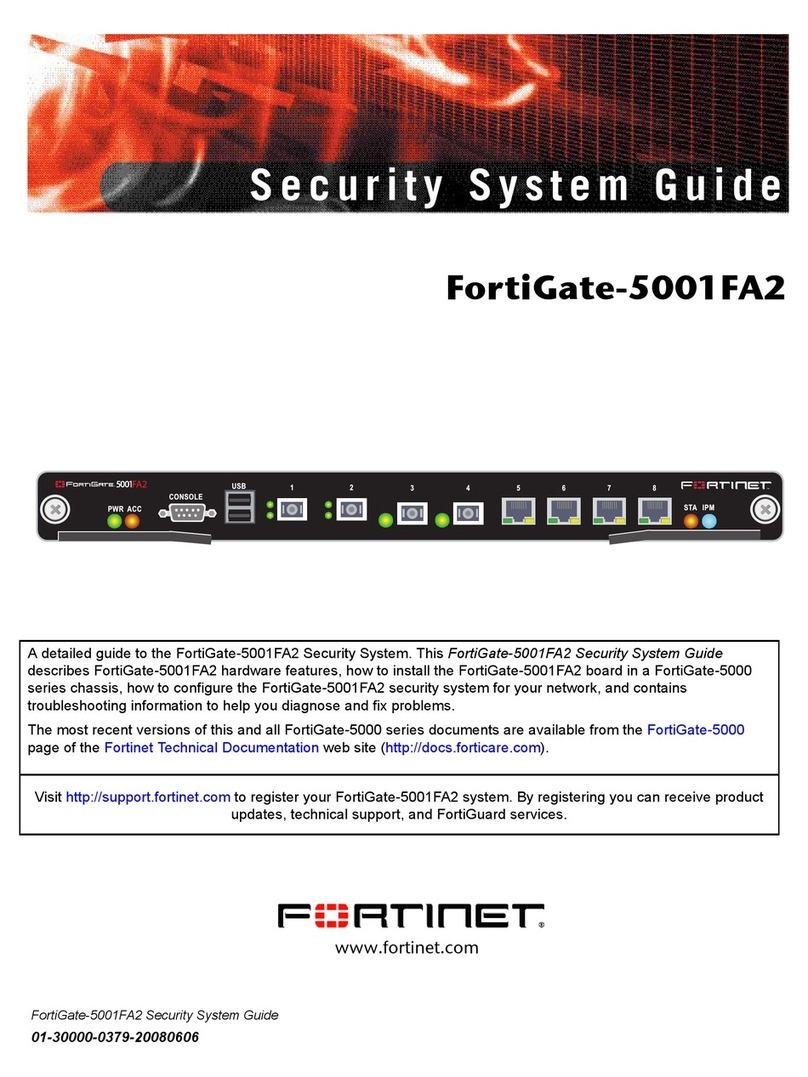
Web-based manager
The FortiGate web-based manager is an easy to use management tool.
Use it to congure the administrator password, the interface and default gateway addresses,
and the DNS server addresses.
Requirements:
• An Ethernet connection between the FortiGate unit and management computer.
• Internet Explorer 6.0 or higher on the management computer.
Command Line Interface (CLI)
The CLI is a full-featured management tool. Use it to congure the administrator password,
the interface addresses, default gateway address, and DNS server addresses. To congure
advanced settings, see the CLI Reference on the Tools and Documentation CD.
Requirements:
• The RJ-45 to DB-9 serial connection between the FortiGate unit and management
computer.
• A terminal emulation application (HyperTerminal for Windows) on the management
computer.