NAT/Route Mode
Port 1 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 2 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 3 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 4 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 5 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 6 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 7 IP: ____.____.____.____
Netmask: ____.____.____.____
Port 8 IP: ____.____.____.____
Netmask: ____.____.____.____
WAN1 IP: ____.____.____.____
Netmask: ____.____.____.____
WAN2 IP: ____.____.____.____
Netmask: ____.____.____.____
The internal interface IP address and netmask must be valid for the internal network.
Transparent mode
Management IP: IP: ____.____.____.____
Netmask: ____.____.____.____
The management IP address and netmask must be valid for the network from which you will manage
the FortiGate unit.
General settings
Administrative account
settings
User name admin
Password (none)
Network Settings Default Gateway: ____.____.____.____
Primary DNS Server: ____.____.____.____
Secondary DNS Server: ____.____.____.____
A default gateway is required for the FortiGate unit to route connections to the Internet.
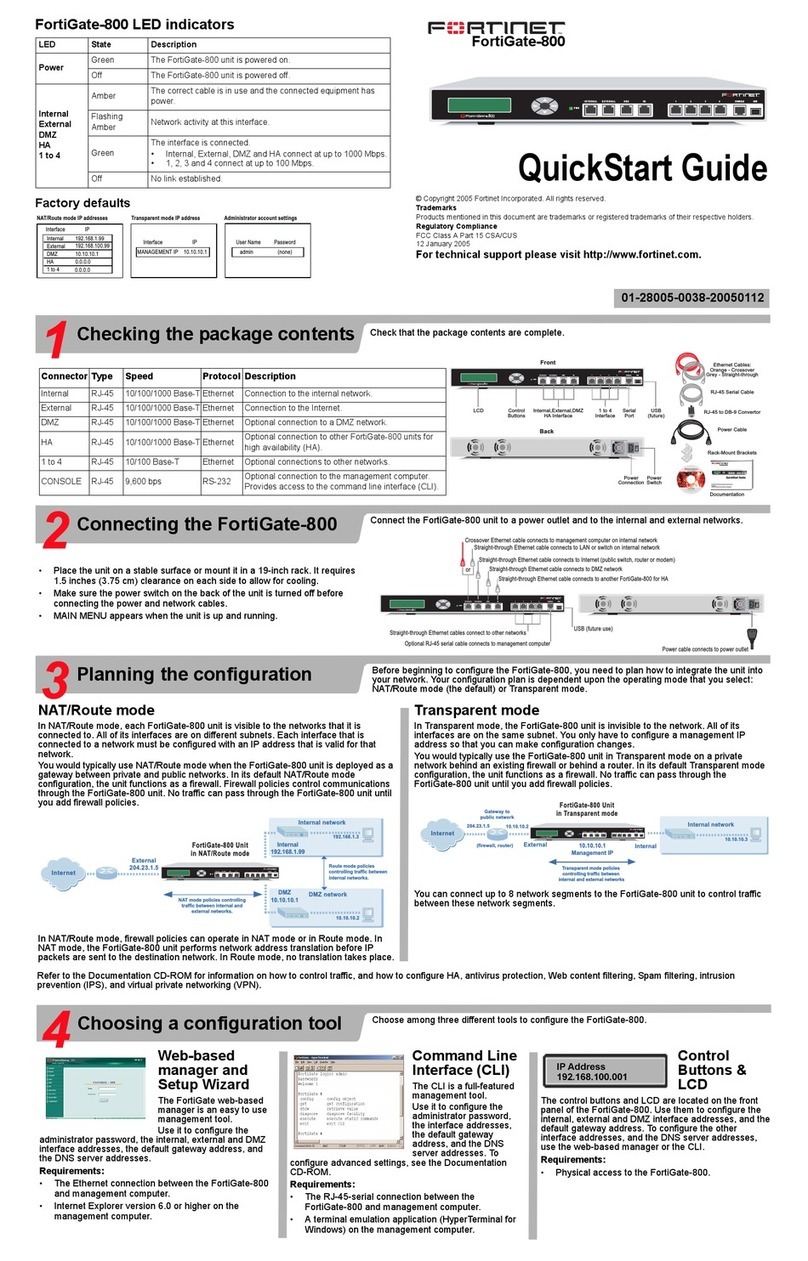
Factory default settings
NAT/Route mode
Internal 192.168.1.99
WAN1
WAN2
DHCP server on Internal interface 192.168.1.110 – 192.168.1.210
To reset the FortiGate unit to the factory defaults, in the CLI type the command
execute factory reset
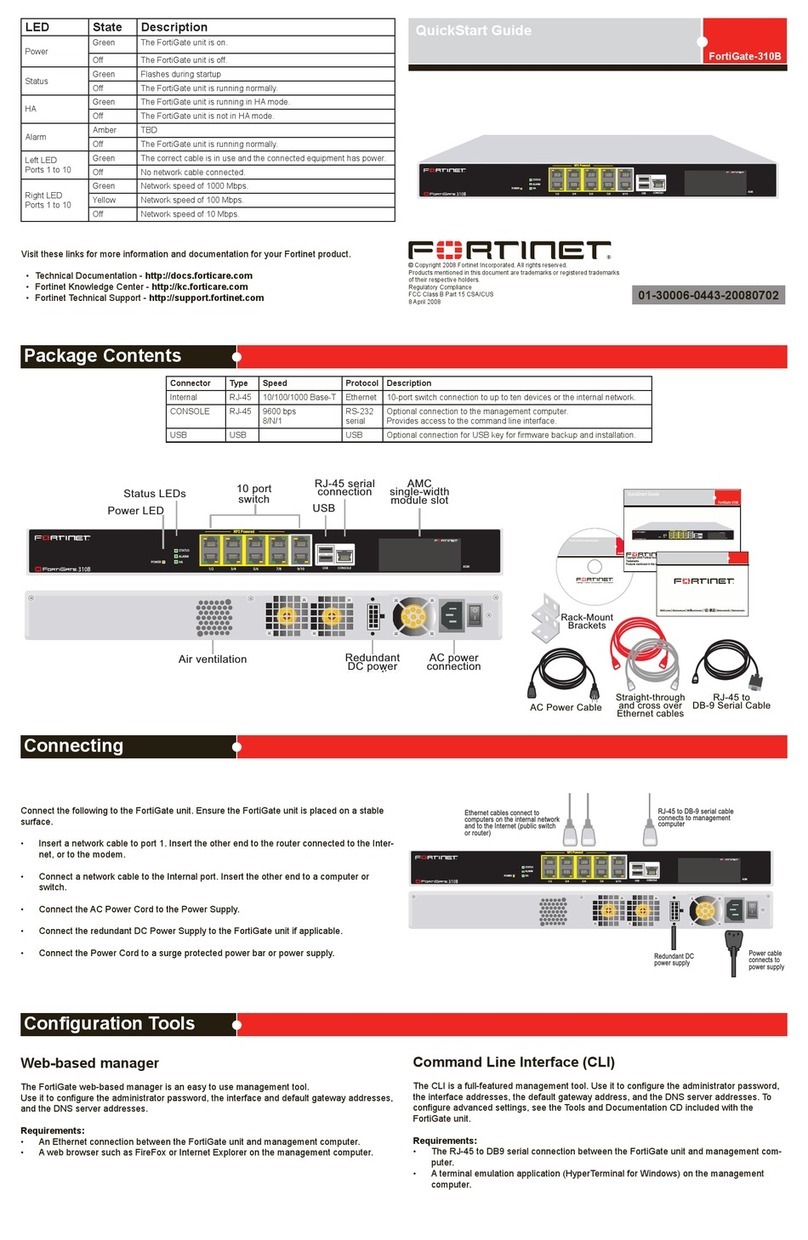
Web Cong
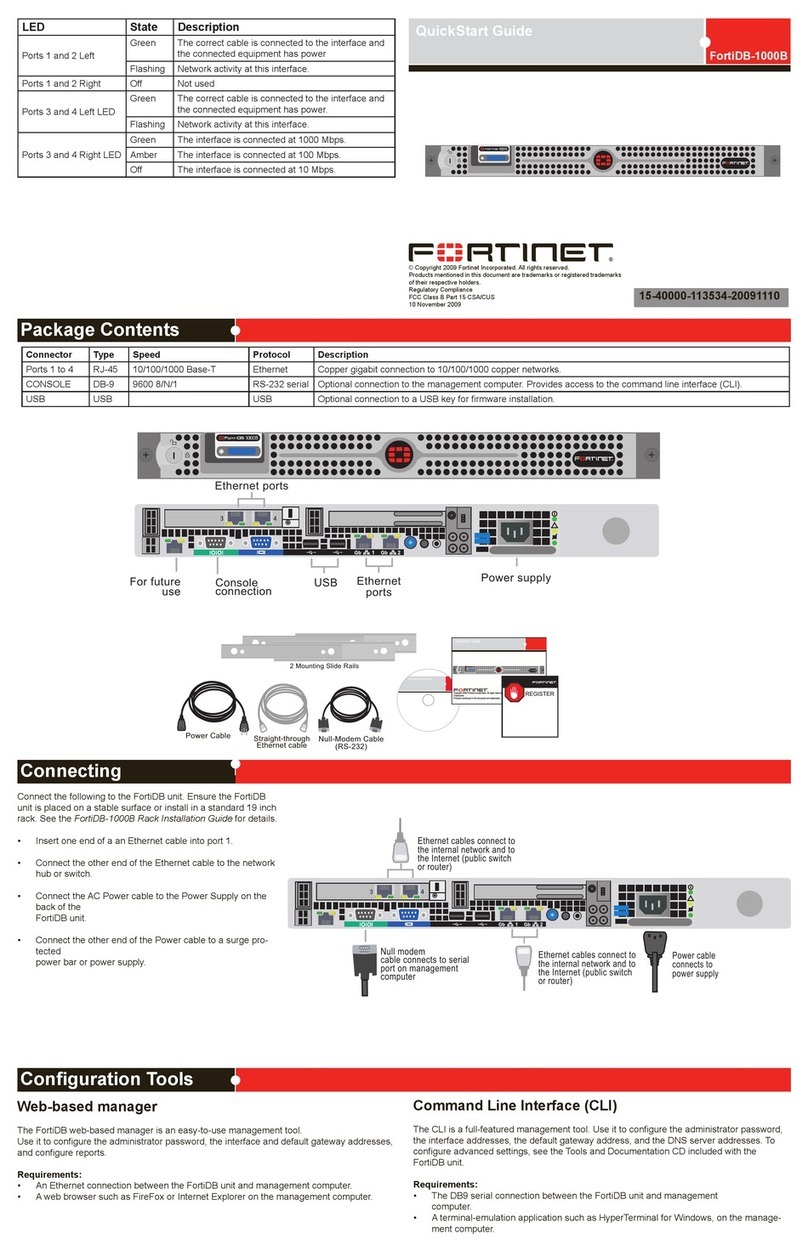
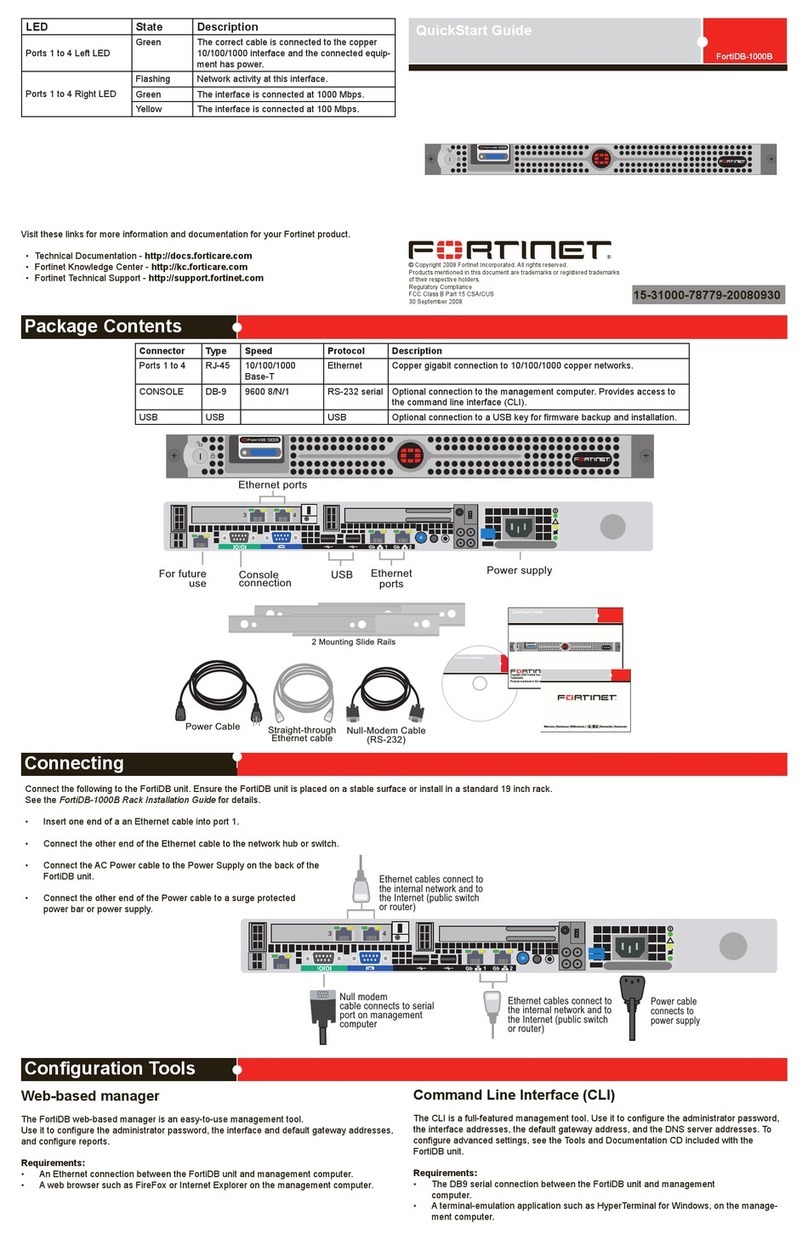
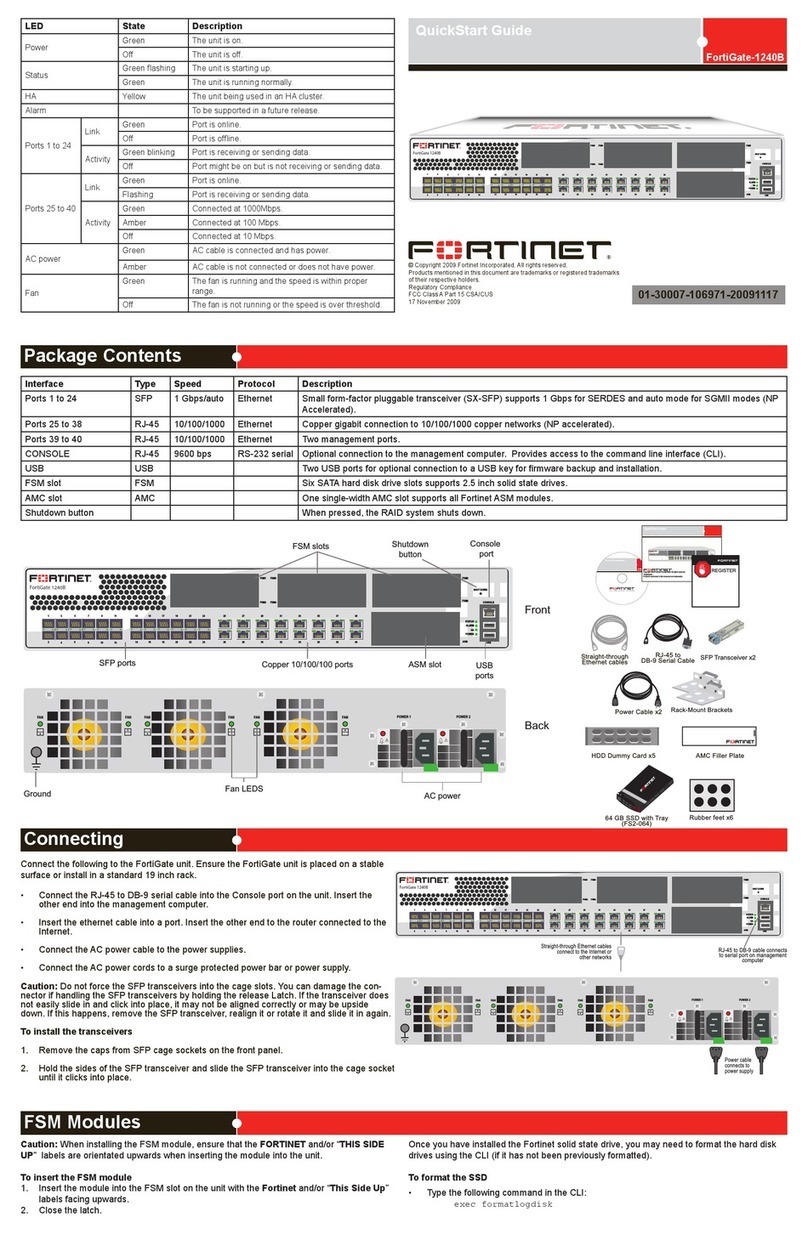
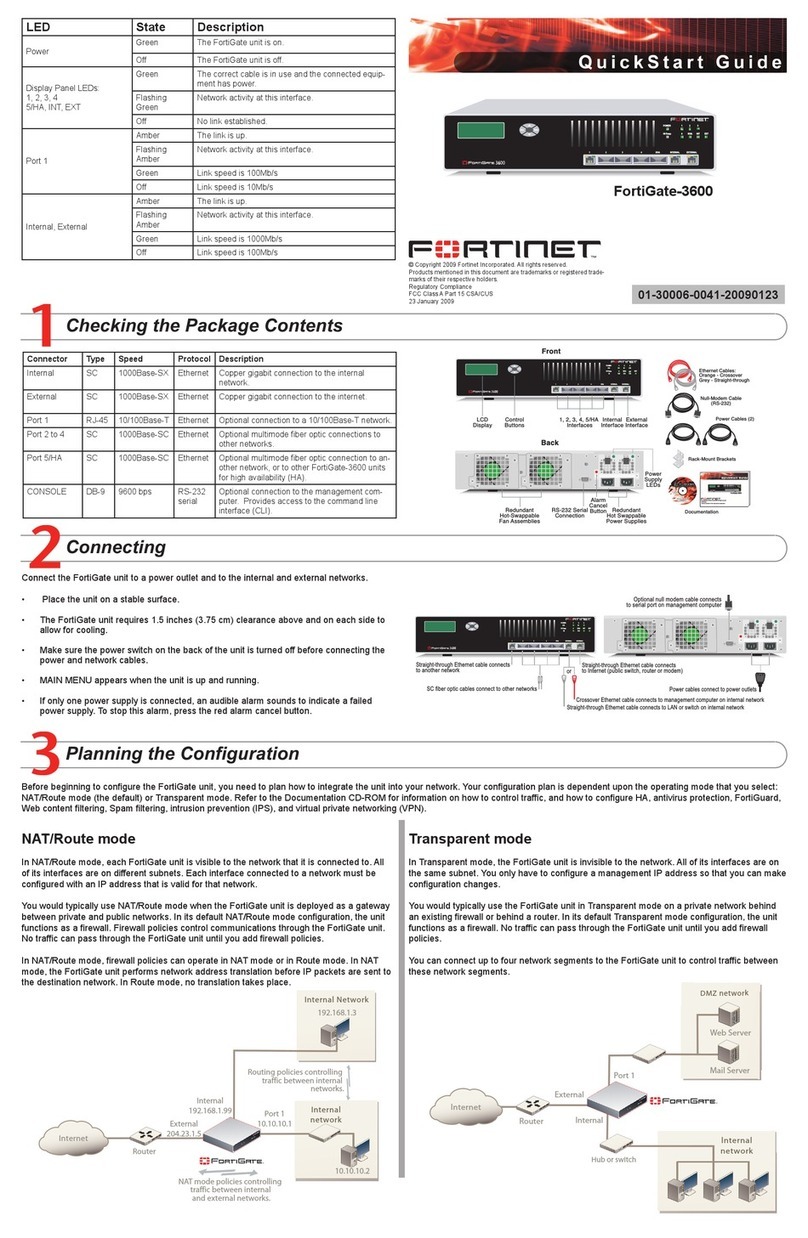
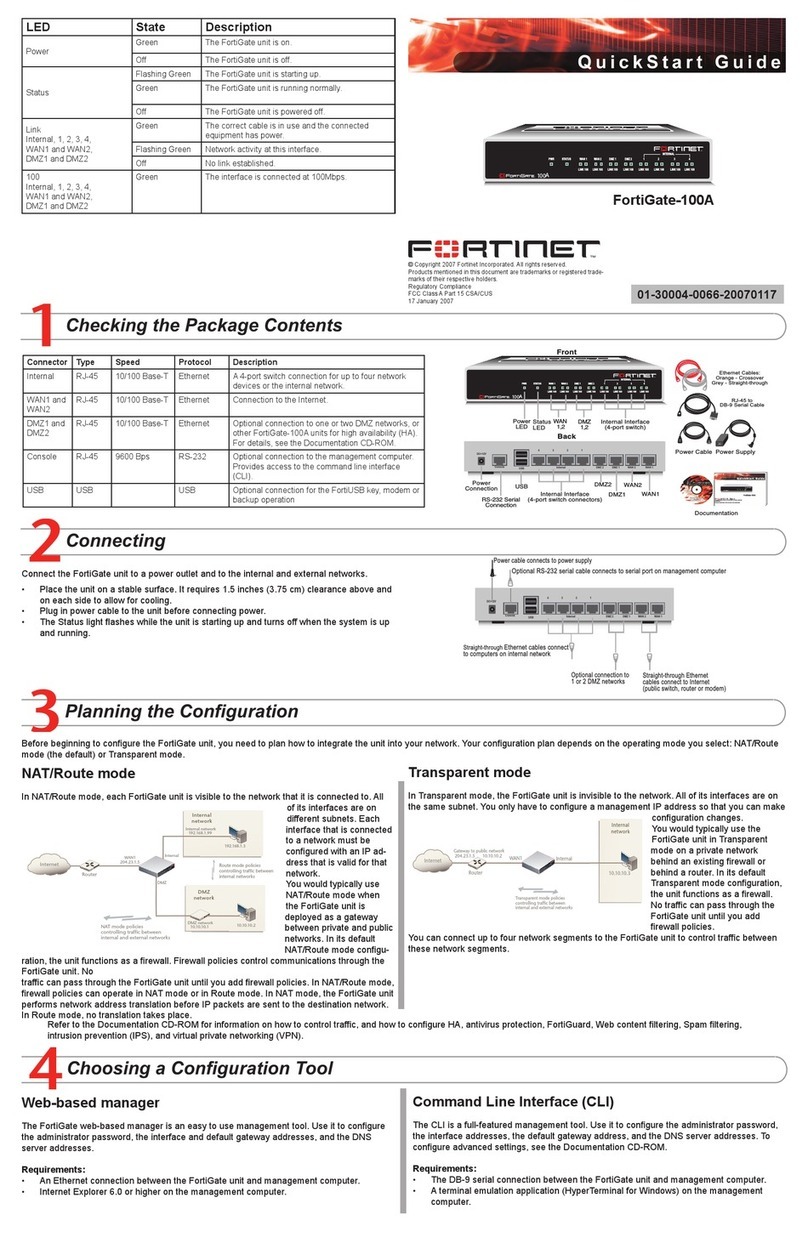
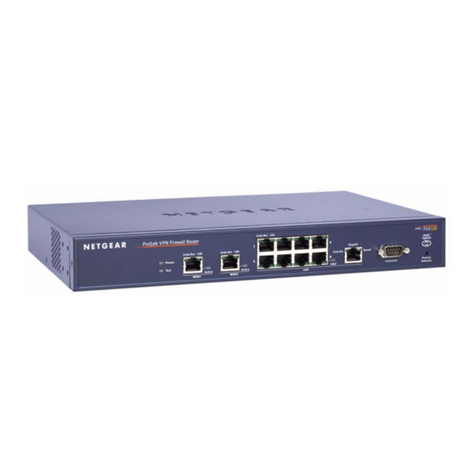
1. Connect the FortiGate internal interface to a management computer Ethernet interface. Use a
cross-over Ethernet cable to connect the devices directly. Use straight-through Ethernet cables to
connect the devices through a hub or switch.
2. Congure the management computer to be on the same subnet as the internal interface of the
FortiGate unit. To do this, change the IP address of the management computer to 192.168.1.2 and
the netmask to 255.255.255.0.
3. To access the FortiGate web-based manager, start Internet Explorer and browse to
https://192.168.1.99 (remember to include the “s” in https://).
4. Type admin in the Name eld and select Login.
NAT/Route mode
To change the administrator password
1. Go to System > Admin > Administrators.
2. Select Change Password for the admin administrator and enter a new password.
To congure interfaces
1. Go to System > Network > Interface.
2. Select the edit icon for each interface to congure.
3. Set the addressing mode for the interface. (See the online help for information.)
• For manual addressing, enter the IP address and netmask for the interface.
• For DHCP addressing, select DHCP and any required settings.
• For PPPoE addressing, select PPPoE, and enter the username and password and any other
required settings.
To congure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > Options, enter the Primary and Secondary DNS IP addresses that you
recorded above and select Apply.
To congure a Default Gateway
1. Go to Router > Static and select Edit icon for the static route.
2. Set Gateway to the Default Gateway IP address you recorded above and select OK.
Transparent mode
To switch from NAT/route mode to transparent mode
1. Go to System > Cong > Operation Mode and select Transparent.
2. Set the Management IP/Netmask to 192.168.1.99/24.
3. Set a default Gateway and select Apply.
To change the administrator password
1. Go to System > Admin > Administrators.
2. Select Change Password for the admin administrator and enter a new password.
To change the management interface
1. Go to System > Cong > Operation Mode.
2. Enter the Management IP address and netmask that you recorded above and select Apply.
To congure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > Options, enter the Primary and Secondary DNS IP addresses that you
recorded above and select Apply.
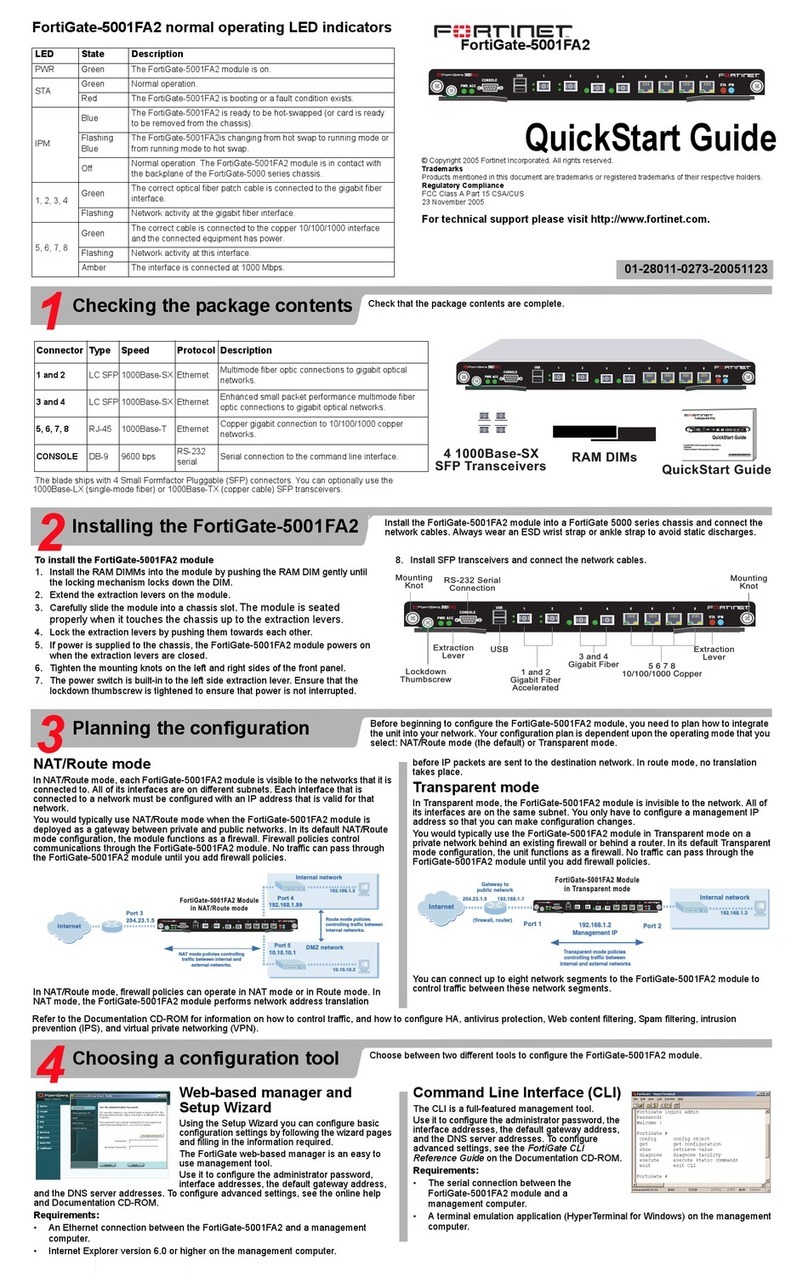
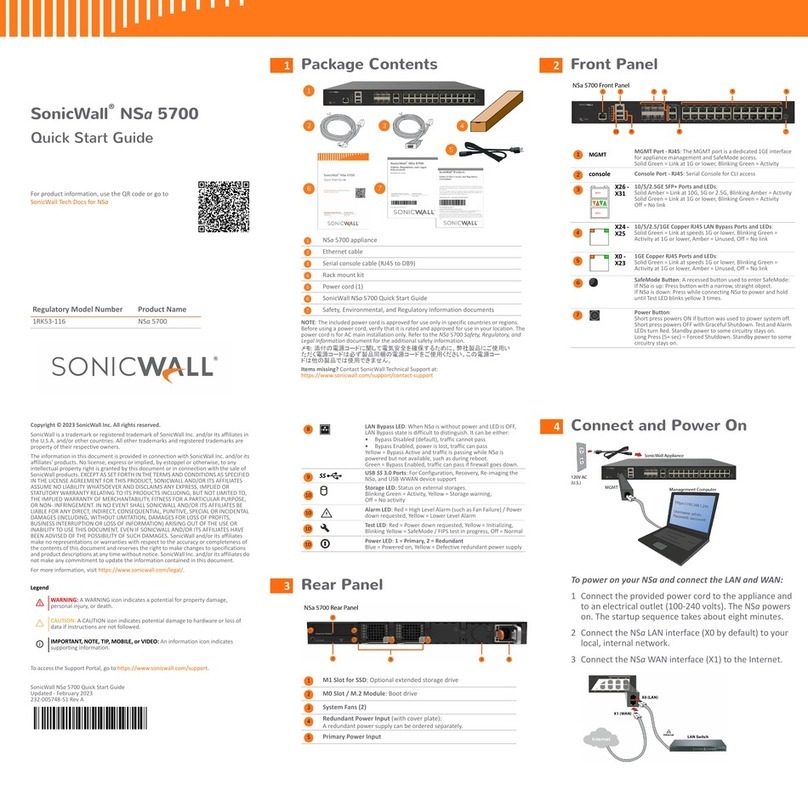
Command Line Interface
1. Use the RJ-45 to DB9 serial cable to connect the FortiGate Console port to the management
computer serial port.
2. Start a terminal emulation program (HyperTerminal) on the management computer. Use these set-
tings:
3. Baud Rate (bps) 9600, Data bits 8, Parity None, Stop bits 1, and Flow Control None.
4. At the Login: prompt, type admin and press Enter twice (no password required).
NAT/Route mode
1. Congure the FortiGate internal interface.
cong system interface
edit internal
set ip <interface_ipv4mask>
end
2. Repeat to congure each interface, for example, to congure the WAN1 interface.
cong system interface
edit wan1
...
3. Congure the primary and secondary DNS server IP addresses.
cong system dns
set primary <dns_ipv4>
set secondary <dns_ipv4>
end
4. Congure the default gateway.
cong router static
edit 1
set gateway <gateway_address_ipv4>
end
Transparent Mode
1. Change from NAT/Route mode to Transparent mode and congure the Management IP address.
cong system settings
set opmode transparent
set manageip <manage_ipv4>
set gateway <gw_ipv4>
end
2. Congure the DNS server IP address.
cong system dns
set primary <dns_ipv4>
set secondary <dns_ipv4>
end
Collecting Information
Conguring
NAT/Route mode
You would typically use NAT/Route mode when the FortiGate unit is deployed as a gateway between
private and public networks. In its default NAT/Route mode conguration, the unit functions as a rewall.
Firewall policies control communications through the FortiGate unit.
Transparent mode
You would typically use the FortiGate unit in Transparent mode on a private network behind an existing
rewall or behind a router. In its default Transparent mode conguration, the unit functions as a rewall.
Conguring PBX Features
Use Web Cong to congure the PBX features below. You will need to congure the following PBX features:
• PSTN Interfaces to establish connection with the telephone network and the FortiGate unit.
• VoIP Provider that provides digital telephone service that uses the Internet for call transport.
• Dial Plan to determine the expected number and pattern of digits for a telephone number. This includes country codes, area codes, and any combination of digits dialed. Dial plans must comply with the
telephone networks to which they connect.
Note that this is only basic conguration information. For more information on conguring the PBX features, see the FortiGate Administration Guide.
To set the PSTN Interfaces
1. Go to System > Network > PSTN Interface tab.
2. Select one of the fxo ports and click the Edit icon to set up the interface.
To set the VoIP Provider
1. Go to PBX > Cong > VoIP Provider tab.
2. Create a VoIP provider and congure the properties.
To set the Dial Plan
1. Go to PBX > Call > Dial Plan tab.
2. Create a new Dial Plan and apply the PSTN Interfaces and/or VoIP Provider to the pattern of digits and the telephone network.