6
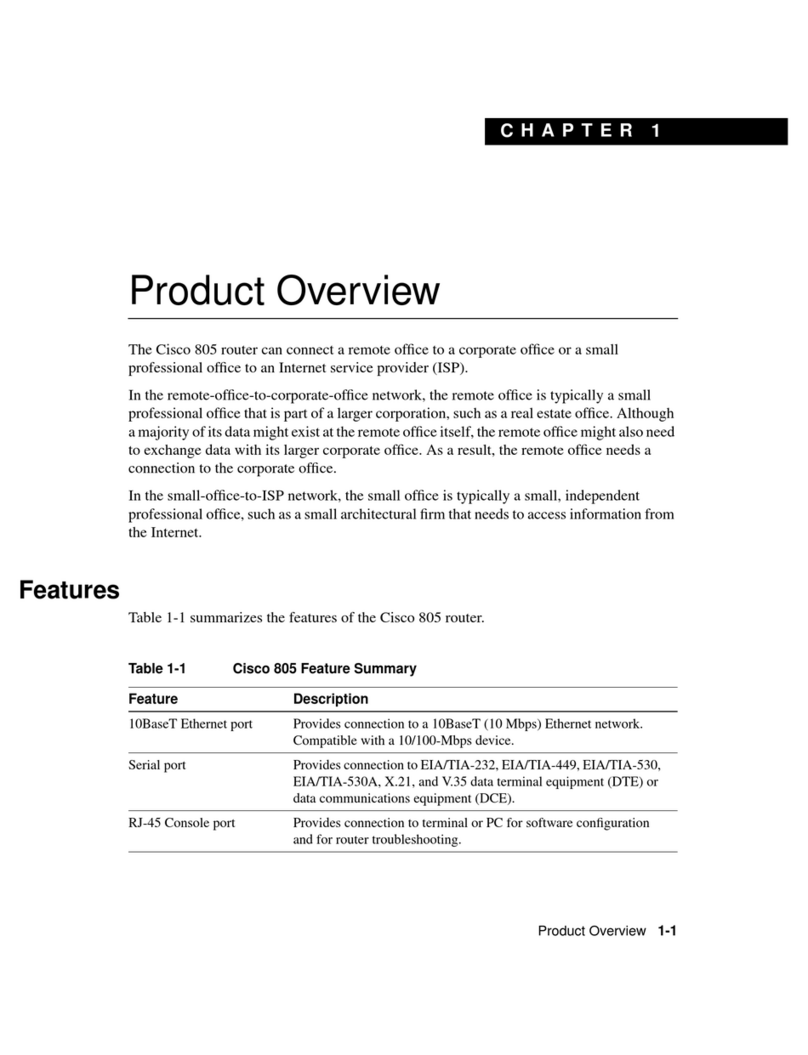
2.4.14 Detailed Statistics.................................................................................................202
2.4.15 DHCP ....................................................................................................................205
2.4.16 DHCP Ser er.........................................................................................................205
2.4.17 Statistics ...............................................................................................................205
2.4.18 Binding .................................................................................................................207
2.4.19 Declined IP ...........................................................................................................208
2.4.20 DHCP Snooping Table...........................................................................................209
2.4.21 DHCP Relay Statistics ...........................................................................................211
2.4.22 DHCP Detailed Statistics ......................................................................................213
2.4.23 Security ................................................................................................................215
2.4.24 Accessment Management Statistics ....................................................................215
2.4.25 Network ...............................................................................................................216
2.4.26 Port Security ........................................................................................................216
2.4.27 Switch...................................................................................................................216
2.4.28 Port ......................................................................................................................218
2.4.29 NAS.......................................................................................................................219
2.4.30 Switch...................................................................................................................219
2.4.31 Port ......................................................................................................................221
2.4.32 ACL Status ............................................................................................................224
2.4.33 ARP Inspection.....................................................................................................226
2.4.34 IP Source Guard ...................................................................................................228
2.4.35 AAA ......................................................................................................................230
2.4.36 RADIUS O er iew.................................................................................................230
2.4.37 RADIUS Details.....................................................................................................232
2.4.38 Switch...................................................................................................................233
2.4.39 RMON ..................................................................................................................233
2.4.40 Statistics ...............................................................................................................233
2.4.41 History..................................................................................................................235
2.4.42 Alarm....................................................................................................................237
2.4.43 E ent ....................................................................................................................238
2.4.44 LACP .....................................................................................................................239
2.4.45 System Status.......................................................................................................239
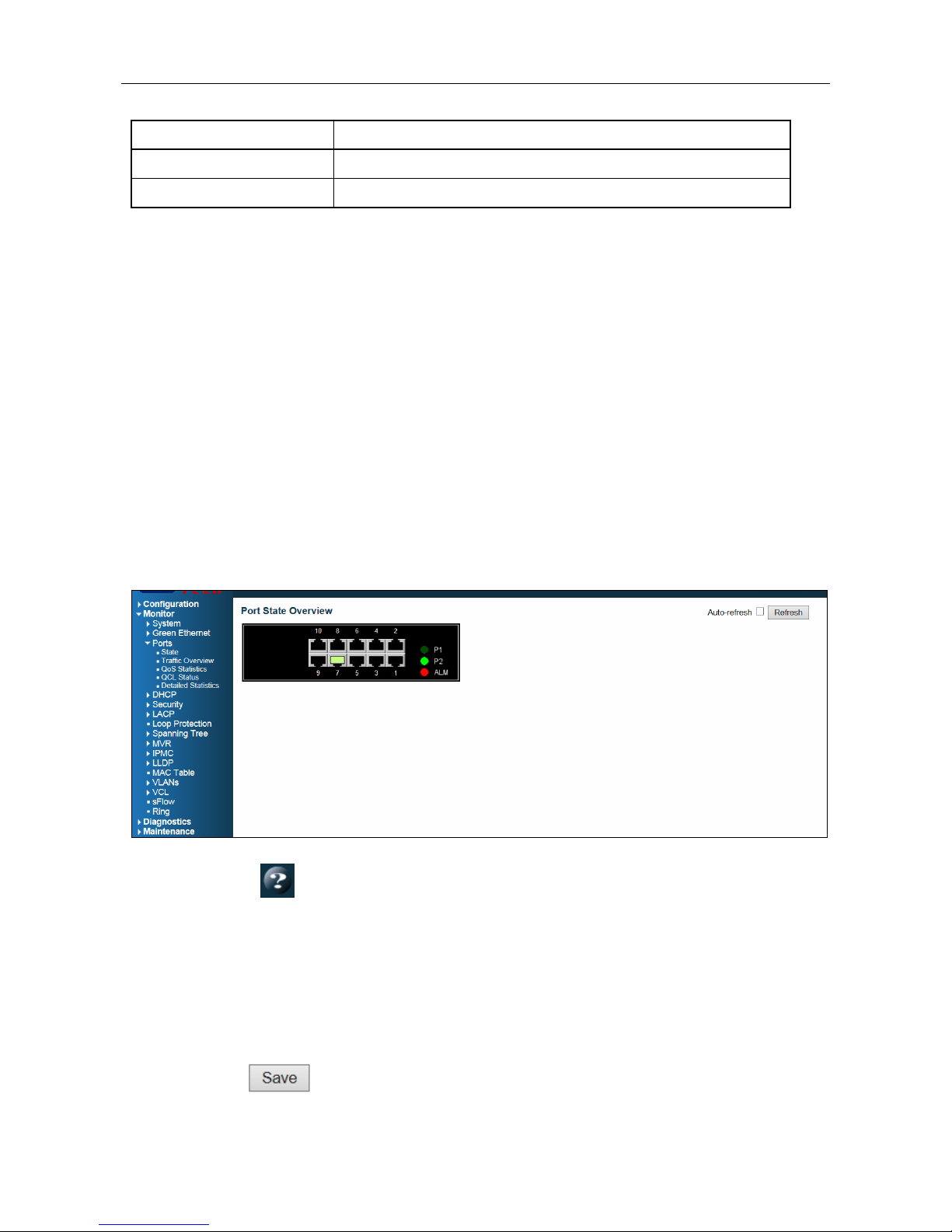
2.4.46 Port Status............................................................................................................240
2.4.47 Port Statistics .......................................................................................................241
2.4.48 Loop Protection ...................................................................................................242
2.4.49 Spanning Tree ......................................................................................................243
2.4.50 Bridge Status........................................................................................................243
2.4.51 Port Status............................................................................................................244