Table of Contents
Installation guide........................................................................................................3
Introduction...........................................................................................................................3
Product overview....................................................................................................................3
The front of the router............................................................................................................................3
...........................................................................................................................................................3
The side of the router.............................................................................................................................4
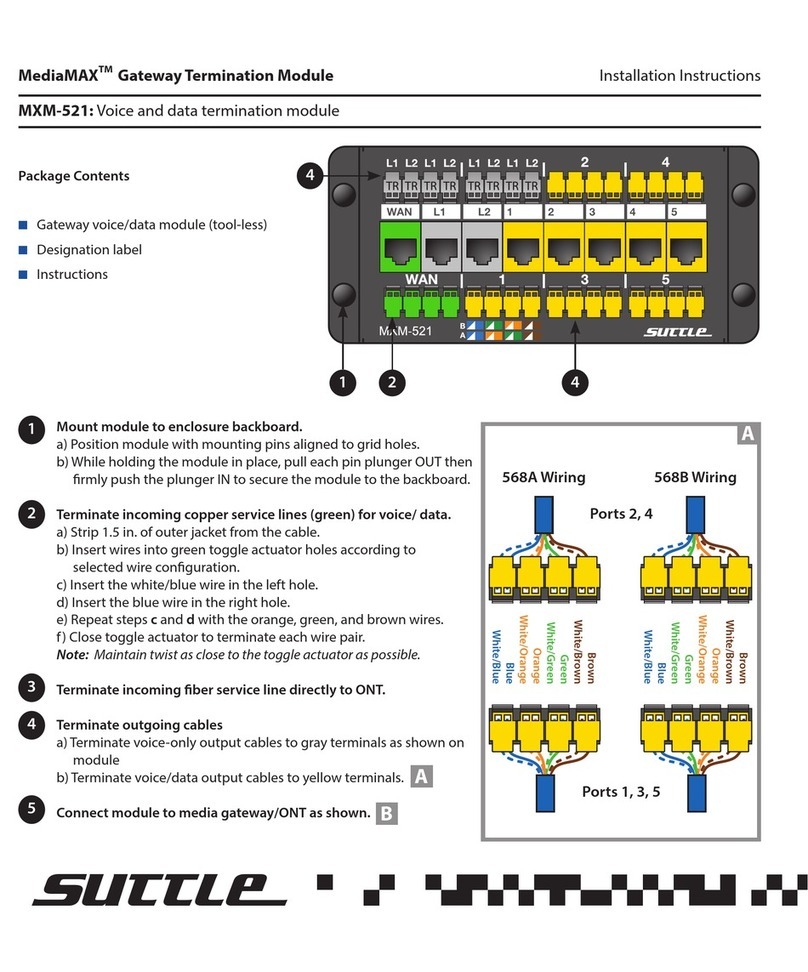
Installation.............................................................................................................................5
Getting started.......................................................................................................................7
Configuring the router (optional)...............................................................................................9
Troubleshooting....................................................................................................................10
Appendix: Router settings.........................................................................................11
Basic...................................................................................................................................11
Network Settings..................................................................................................................................11
Advanced ............................................................................................................................14
Virtual Server......................................................................................................................................14
Special Applications .............................................................................................................................15
Port Forwarding....................................................................................................................................16
Routing...............................................................................................................................................16
Access Control.....................................................................................................................................17
Website Filter.......................................................................................................................................17
Firewall Settings...................................................................................................................................18
Inbound Filter......................................................................................................................................20
Advanced Network................................................................................................................................21
Tools ..................................................................................................................................22
Administrator Settings..........................................................................................................................22
Time...................................................................................................................................................22
System...............................................................................................................................................23
Dynamic DNS......................................................................................................................................23
System Check......................................................................................................................................23
Schedules...........................................................................................................................................24
Status .................................................................................................................................25
Device Info..........................................................................................................................................25
Routing...............................................................................................................................................25
Logs...................................................................................................................................................25
Statistics.............................................................................................................................................25
Internet Sessions.................................................................................................................................26
Firewall Holes......................................................................................................................................26
Copyright © Genexis BV. All rights reserved 2