Table of contents
1 Introduction ........................................................................................................................................... 5
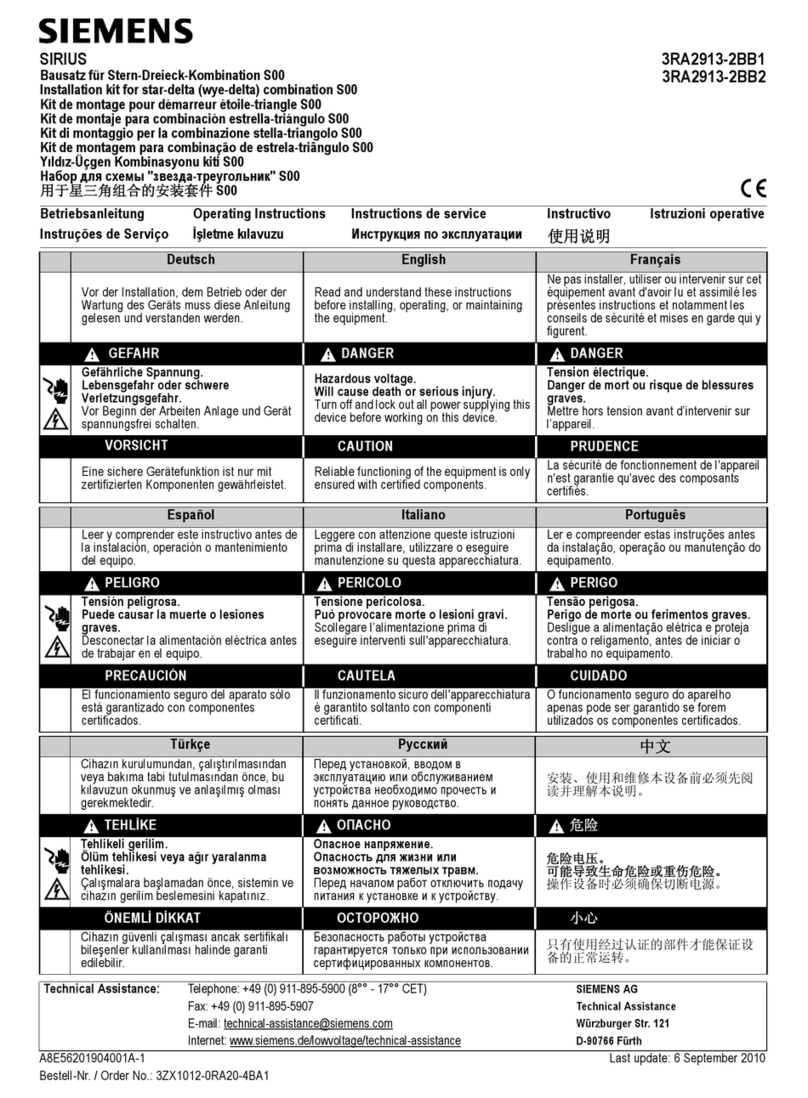
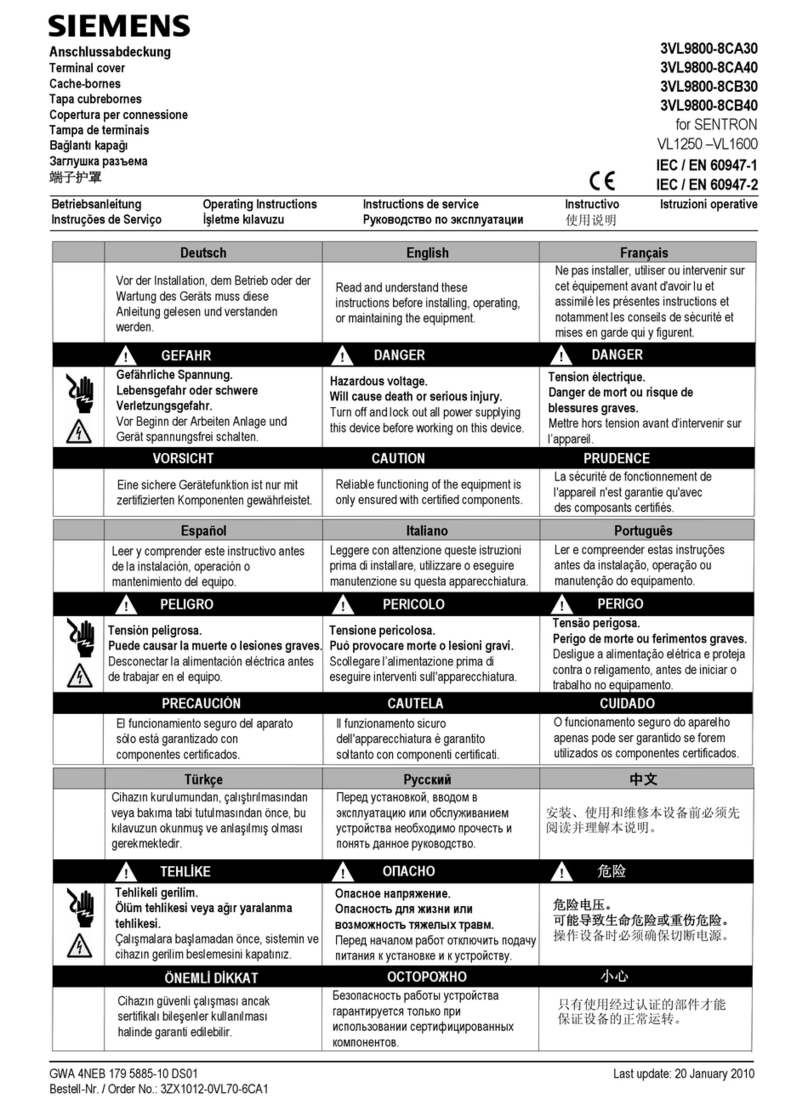
2 Safety notices ........................................................................................................................................ 9
3 Security recommendations.................................................................................................................. 11
4 Description of the device..................................................................................................................... 17
4.1 Device view ....................................................................................................................... 18
4.2 Components of the product ............................................................................................... 19
4.3 Accessories........................................................................................................................ 20
4.3.1 Installation ........................................................................................................................ 20
4.3.2 CLP.................................................................................................................................... 20
4.3.3 Industrial Ethernet ............................................................................................................. 21
4.3.4 Digital input / digital output ............................................................................................... 22
4.3.5 Power supply ..................................................................................................................... 23
4.3.6 Flexible connecting cables and antennas............................................................................ 24
4.3.6.1 Flexible connecting cables ................................................................................................. 24
4.3.6.2 Lightning protection .......................................................................................................... 25
4.3.6.3 Terminating resistor ........................................................................................................... 26
4.3.6.4 Antennas........................................................................................................................... 26
4.4 LED display ........................................................................................................................ 28
4.5 Reset button ...................................................................................................................... 32
5 Mounting ............................................................................................................................................. 33
5.1 Types of installation ........................................................................................................... 36
5.2 Wall mounting................................................................................................................... 37
5.3 Mounting on VESA bracket ................................................................................................ 38
5.4 DIN rail mounting .............................................................................................................. 39
5.4.1 Installation with the DIN rail mounting adapter .................................................................. 39
5.4.2 Mounting with bracket support .......................................................................................... 41
6 Connection........................................................................................................................................... 45
6.1 Power supply ..................................................................................................................... 50
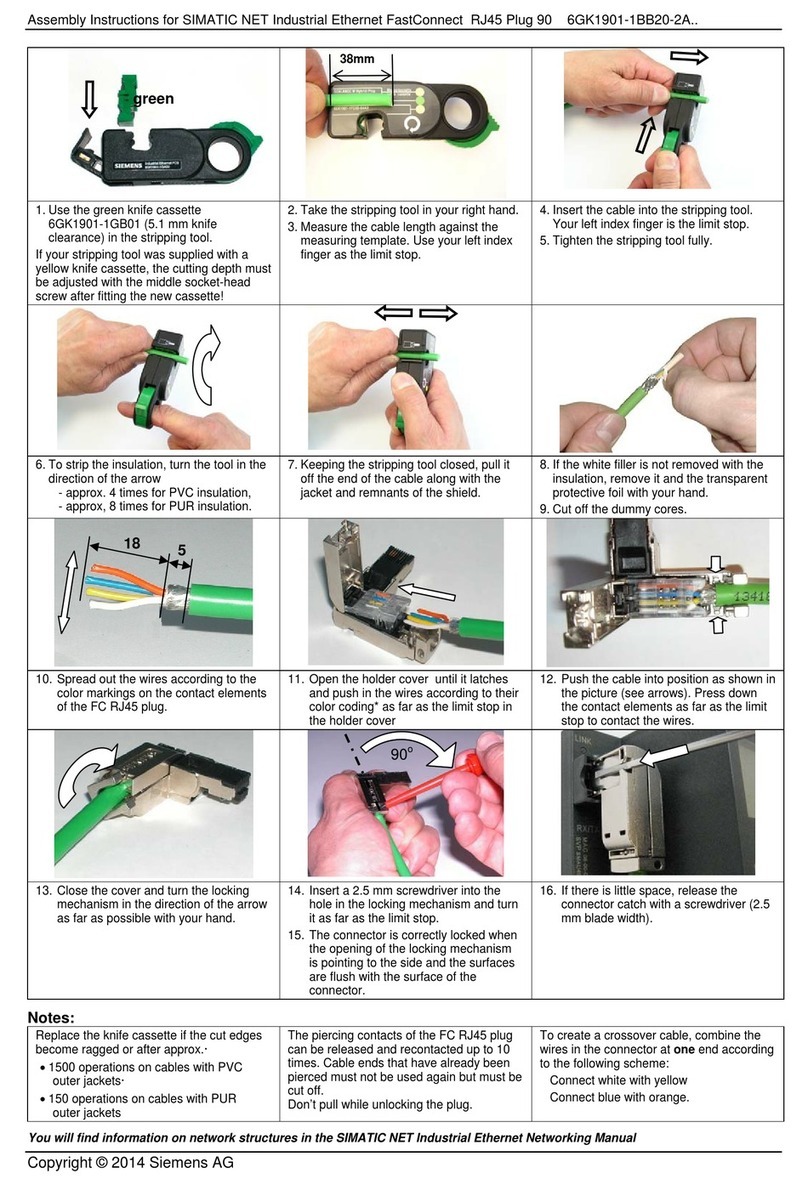
6.2 Ethernet ............................................................................................................................ 52
6.3 Antenna connector ............................................................................................................ 53
6.4 Grounding ......................................................................................................................... 55
6.5 Digital input/output ........................................................................................................... 56
6.6 Inserting/removing the PLUG.............................................................................................. 57
7 Upkeep and maintenance.................................................................................................................... 61
7.1 Downloading new rmware using TFTP without WBM and CLI............................................. 61
SCALANCE WxM766
Operating Instructions, 07/2021, C79000-G8976-C617-02 3