Symbols
Convention Description
Means reader be extremely careful. Improper operation may cause
bodily injury.
Means reader be careful. Improper operation may cause data loss or
damage to equipment.
Means an action or information that needs special attention to ensure
successful configuration or good performance.
Means a complementary description.
Means techniques helpful for you to make configuration with ease.
Related Documentation
In addition to this manual, each H3C S5500-EI Series Ethernet Switch documentation set includes the
following:
Manual Description
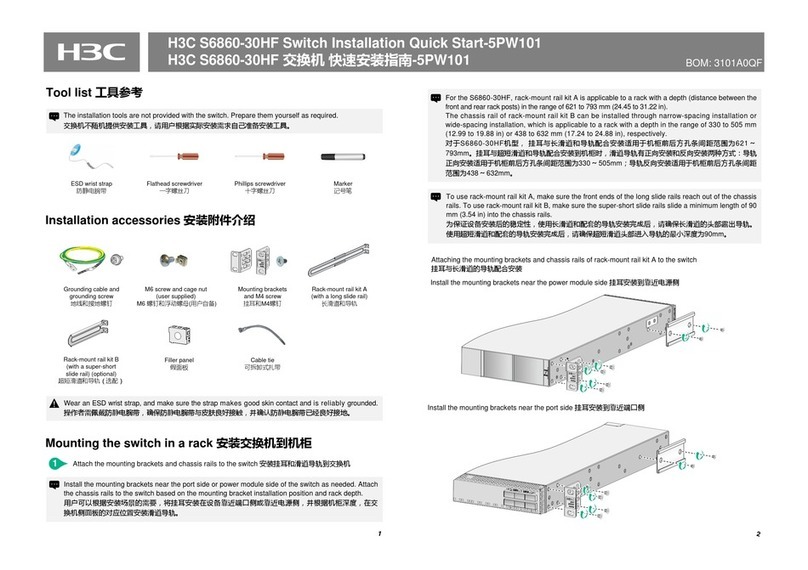
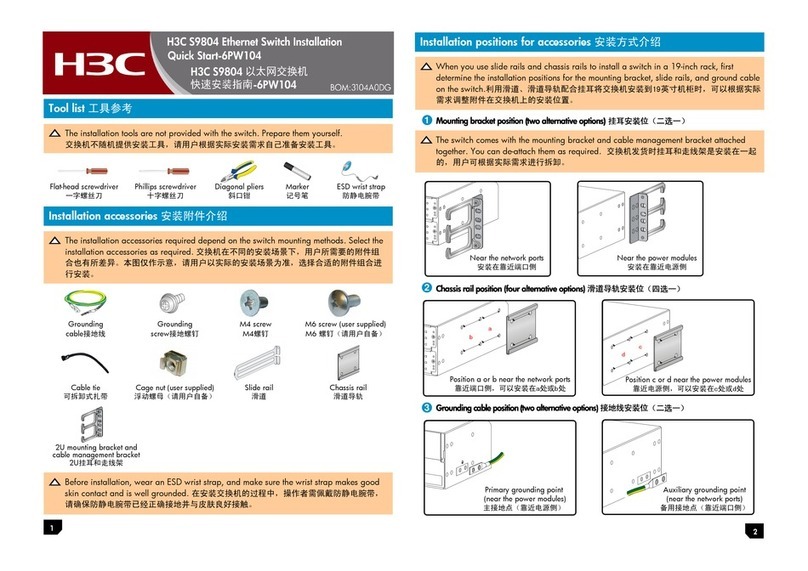
H3C S5500-EI Series Ethernet Switches
Installation Manual
It introduces the installation procedure,
commissioning, maintenance and monitoring of
the S5500-EI Series Ethernet switches.
H3C S5500-EI Series Ethernet Switches
Command Manual - Release 2202
It includes Feature List and Command Index,
Access Volume, IP Services Volume, IP Routing
Volume, IP Multicast Volume, QoS Volume,
Security Volume and System Volume
commands.
Obtaining Documentation
You can access the most up-to-date H3C product documentation on the World Wide Web at this URL:
http://www.h3c.com.
The following are the columns from which you can obtain different categories of product documentation:
[Products & Solutions]: Provides information about products and technologies, as well as solutions.
[Technical Support & Document > Technical Documents]: Provides several categories of product
documentation, such as installation, operation, and maintenance.
[Technical Support & Document > Product Support > Software]: Provides the documentation released
with the software version.
Documentation Feedback
We appreciate your comments.