Cisco ASA 55 Series Quick start guide
Other Cisco Security System manuals

Cisco
Cisco WVC200 - Wireless-G PTZ Internet Camera Instruction Manual
Cisco
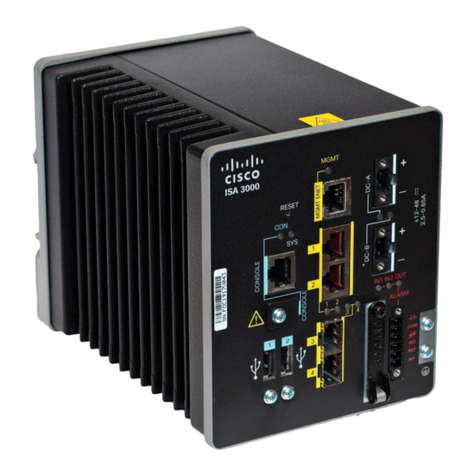
Cisco ISA 3000 User manual

Cisco
Cisco Firepower 1100 Series User manual

Cisco
Cisco Meraki MX67 User manual

Cisco
Cisco Codec C Series User manual
Cisco
Cisco MARS Instructions for use
Cisco
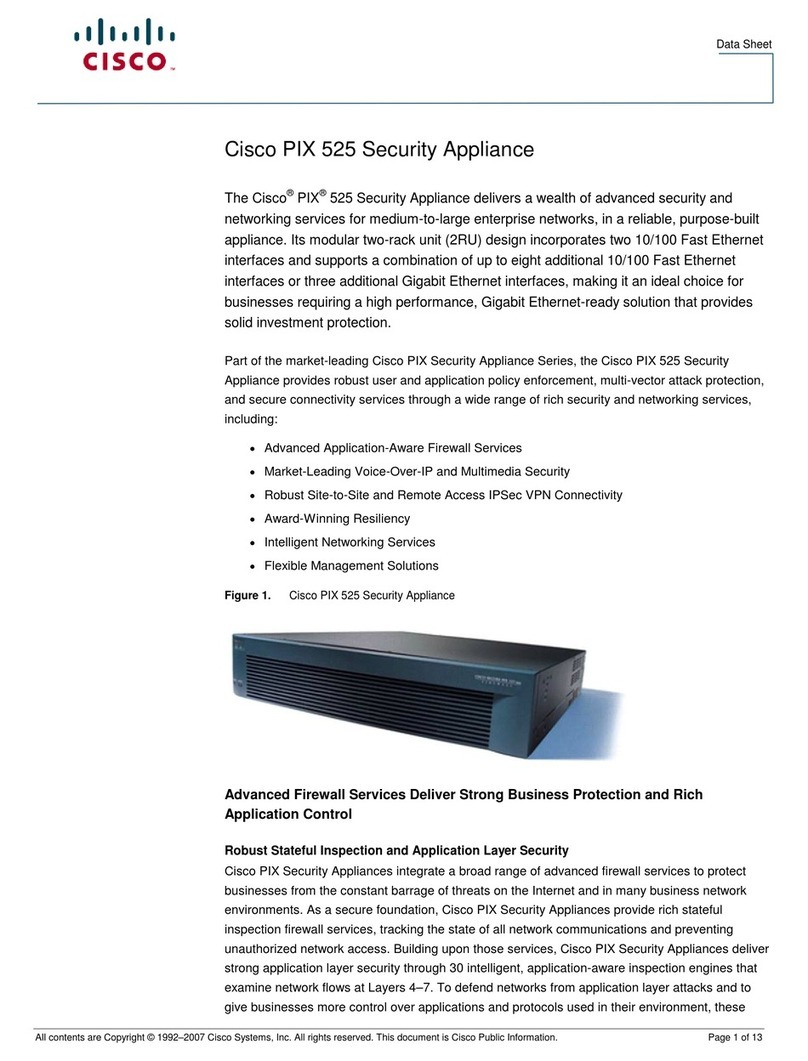
Cisco PIX 525 User manual
Cisco
Cisco MEDVIEW-C-30XS-A01 User manual
Cisco
Cisco M5 User manual

Cisco
Cisco Small Business Pro SA 500 Series User manual

Cisco
Cisco ISA550 User manual

Cisco
Cisco Telepresence MX200 Instruction Manual

Cisco
Cisco ASA 5506W-X Manual
Cisco
Cisco C195 Quick start guide

Cisco
Cisco NCS 4000 Series User manual

Cisco
Cisco IronPort S670 User manual

Cisco
Cisco 500 Series User manual

Cisco
Cisco ISA550 Instruction Manual
Cisco
Cisco C395 Manual
Cisco
Cisco 4116 - EtherFast Switch Guide
Popular Security System manuals by other brands

Inner Range
Inner Range Concept 2000 user manual
Climax
Climax Mobile Lite R32 Installer's guide

FBII
FBII XL-31 Series installation instructions
Johnson Controls
Johnson Controls PENN Connected PC10 Install and Commissioning Guide

Aeotec
Aeotec Siren Gen5 quick start guide
IDEAL
IDEAL Accenta Engineering information
Swann
Swann SW-P-MC2 Specifications
Ecolink
Ecolink Siren+Chime user manual
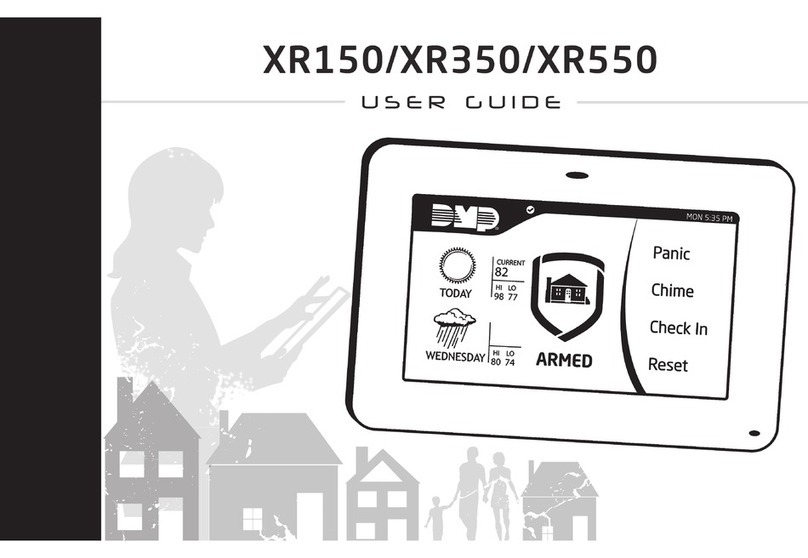
Digital Monitoring Products
Digital Monitoring Products XR150 user guide
EDM
EDM Solution 6+6 Wireless-AE installation manual

Siren
Siren LED GSM operating manual
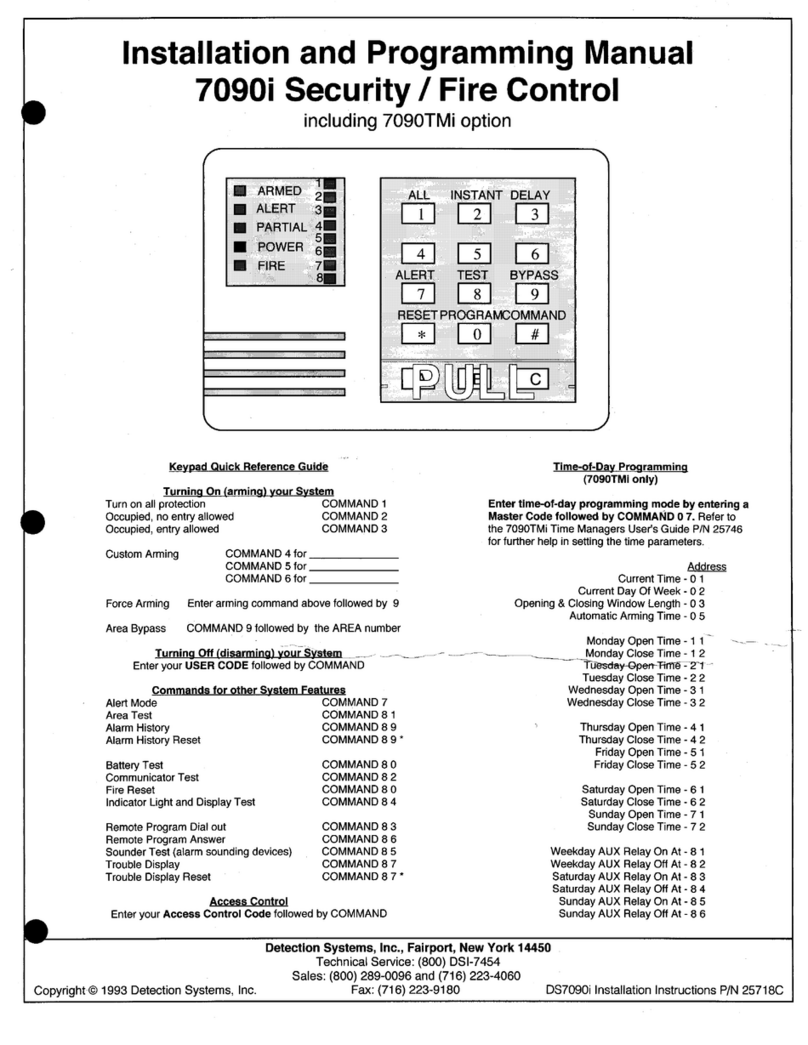
Detection Systems
Detection Systems 7090i Installation and programming manual