Dahua DSS7016D-S2 User manual
Other Dahua Security System manuals
Dahua
Dahua DSS4004-S2 User guide
Dahua
Dahua Smart Professional Surveillance System User manual
Dahua
Dahua ARA10-W User manual

Dahua
Dahua ARC6416C series User manual

Dahua
Dahua DHI-ARA12-W2 User manual

Dahua
Dahua DHI-ARC3008C User guide
Dahua
Dahua VTH1200 Series User manual

Dahua
Dahua DSS4004 User manual

Dahua
Dahua DHI-XVR5432L-X User manual
Dahua
Dahua 8-HDD Series User manual
Popular Security System manuals by other brands

Inner Range
Inner Range Concept 2000 user manual
Climax
Climax Mobile Lite R32 Installer's guide

FBII
FBII XL-31 Series installation instructions
Johnson Controls
Johnson Controls PENN Connected PC10 Install and Commissioning Guide

Aeotec
Aeotec Siren Gen5 quick start guide
IDEAL
IDEAL Accenta Engineering information
Swann
Swann SW-P-MC2 Specifications
Ecolink
Ecolink Siren+Chime user manual
Digital Monitoring Products
Digital Monitoring Products XR150 user guide
EDM
EDM Solution 6+6 Wireless-AE installation manual

Siren
Siren LED GSM operating manual
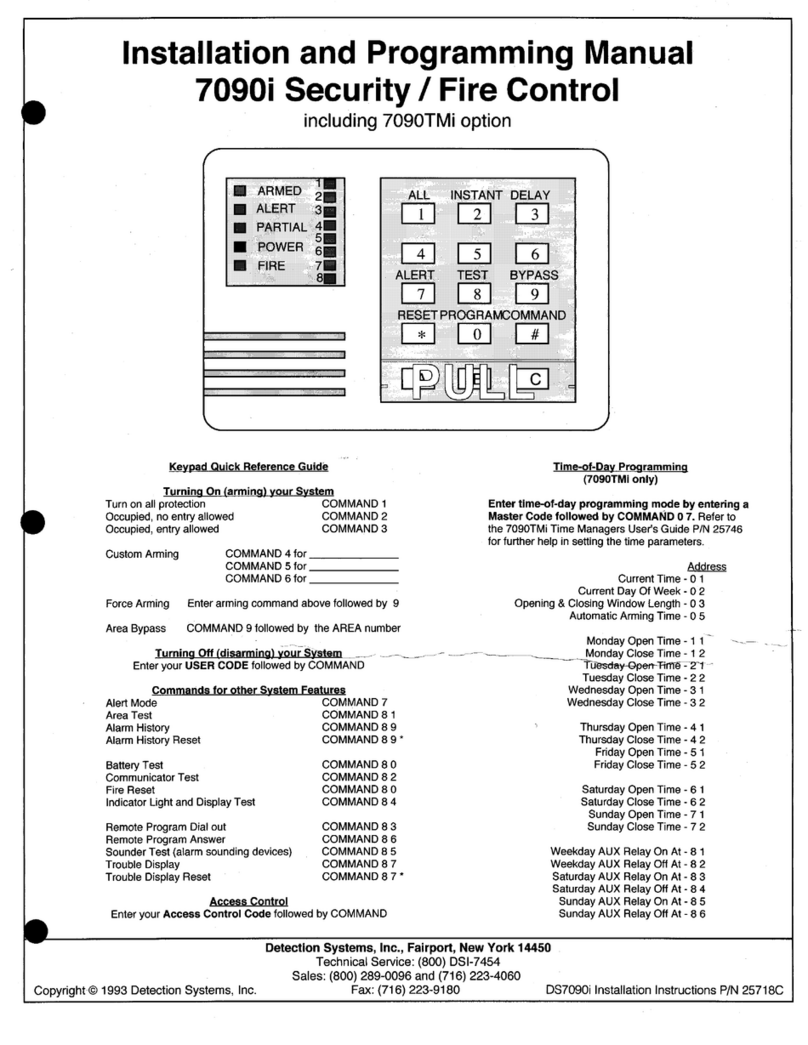
Detection Systems
Detection Systems 7090i Installation and programming manual