©©2004, Avaya Inc.2004, Avaya Inc.
All Rights Reserved, Printed in All Rights Reserved, Printed in U.S.A.U.S.A.
NoticeNotice
Every effort was made to ensure that the information in this book was complete and accurate at the tiEvery effort was made to ensure that the information in this book was complete and accurate at the ti me of printing. me of printing. However, information is subject toHowever, information is subject to
change.change.
Avaya Web PageAvaya Web Page
The world wide web home pThe world wide web home page for Avaya is: age for Avaya is: http://www.avaya.comhttp://www.avaya.com
Preventing Toll FraudPreventing Toll Fraud
Toll Fraud is the Toll Fraud is the unauthorized use of your telecommunications system by an unauthorized use of your telecommunications system by an unauthorized party (for example, a person who is unauthorized party (for example, a person who is not a corporate employee,not a corporate employee,
agent, subcontractor, or working on your comagent, subcontractor, or working on your company’s behalf). pany’s behalf). Be aware that there is a risk of toll Be aware that there is a risk of toll fraud associated with your system and that, if toll fraudfraud associated with your system and that, if toll fraud
occurs, it can result in substantial additional charges for your telecommunications services.occurs, it can result in substantial additional charges for your telecommunications services.
Avaya Fraud InterventionAvaya Fraud Intervention
If you sIf you suspect that you are uspect that you are being victimizedbeing victimizedby toll fraud and you need technical assistance or support, call the Technical Service Center’s Toll Fraudby toll fraud and you need technical assistance or support, call the Technical Service Center’s Toll Fraud
Intervention Hotline at Intervention Hotline at 1.800.643.231.800.643.2353.53.
Providing Telecommunications SecurityProviding Telecommunications Security
Telecommunications security of voice, data, and/or video communications is the prevention of any type of intrusion to, that is, either unauthorized orTelecommunications security of voice, data, and/or video communications is the prevention of any type of intrusion to, that is, either unauthorized or
malicious access to malicious access to or use of, your company’s telecommunications equipment by some party.or use of, your company’s telecommunications equipment by some party.
Your company’s “telecommunications equipment” includes both this Your company’s “telecommunications equipment” includes both this Avaya product and any other voice/data/video equipment that Avaya product and any other voice/data/video equipment that could be accessed viacould be accessed via
this Avaya product (that is, this Avaya product (that is, “networked equipment”).“networked equipment”).
An “outside party” is anyone who is not a corporate employee, agent, subcontractor, or a person working on your comAn “outside party” is anyone who is not a corporate employee, agent, subcontractor, or a person working on your company’s behalf. pany’s behalf. Whereas, aWhereas, a
“malicious party” is Anyone, including someone who may be “malicious party” is Anyone, including someone who may be otherwise authorized, who accesses your telecotherwise authorized, who accesses your telecommunications equipment with eitherommunications equipment with either
malicious or mischievous intent.malicious or mischievous intent.
Such intrusions may be either to/tSuch intrusions may be either to/through synchronous (time-multiplexed and/or circuit-based) or asynchronous (character-, message-, or packet-based)hrough synchronous (time-multiplexed and/or circuit-based) or asynchronous (character-, message-, or packet-based)
equipment or interfaces for reasons of:equipment or interfaces for reasons of:
•• Utilization (of capabilities special to the accessed equipment)Utilization (of capabilities special to the accessed equipment)
•• Theft (such as, of intellectual property, financial assets, or toll-facility access)Theft (such as, of intellectual property, financial assets, or toll-facility access)
•• Eavesdropping (privacy invasions to humans)Eavesdropping (privacy invasions to humans)
•• Mischief (troubling, but apparently innocuous, tampering)Mischief (troubling, but apparently innocuous, tampering)
•• Harm (such as harmful tampering, data loss or alteration, regardless of motive or intent)Harm (such as harmful tampering, data loss or alteration, regardless of motive or intent)
Be aware that there could be a risk of unauthorized intrusions associated with your system and/or its networked equipment. Be aware that there could be a risk of unauthorized intrusions associated with your system and/or its networked equipment. Also realize that, if such anAlso realize that, if such an
intrusion should occur, it could result in a variety of losses to your company, including but not limited to, human/data privacy, intellectual property,intrusion should occur, it could result in a variety of losses to your company, including but not limited to, human/data privacy, intellectual property,
material assets, financial resources, labor costs, and/or legal costs).material assets, financial resources, labor costs, and/or legal costs).
Your Responsibility for Your Company’s Telecommunications SecurityYour Responsibility for Your Company’s Telecommunications Security
The final responsibility for securing both tThe final responsibility for securing both t his system and its his system and its networked equipment rests with you – an networked equipment rests with you – an Avaya customer’s system administrator, yourAvaya customer’s system administrator, your
telecommunications peers, and your managers. telecommunications peers, and your managers. Base the fulfillment of your responsibility on acquired knowledge and resources from a variety of sourcesBase the fulfillment of your responsibility on acquired knowledge and resources from a variety of sources
including but not limited to:including but not limited to:
•• Installation documentsInstallation documents
•• System administration documentsSystem administration documents
•• Security documentsSecurity documents
•• Hardware-/software-based security toolsHardware-/software-based security tools
•• Shared information between you and your peersShared information between you and your peers
•• Telecommunications security expertsTelecommunications security experts
To prevent intrusions to your telecommunications eTo prevent intrusions to your telecommunications e quipment, you and your peers should carefully program and configure your:quipment, you and your peers should carefully program and configure your:
•• Avaya provided telecommunications systems and their interfacesAvaya provided telecommunications systems and their interfaces
•• Avaya provided software applications, as well as Avaya provided software applications, as well as their underlying hardware/ software platforms and interfacestheir underlying hardware/ software platforms and interfaces
•• Any other equipment networked to your Avaya productsAny other equipment networked to your Avaya products
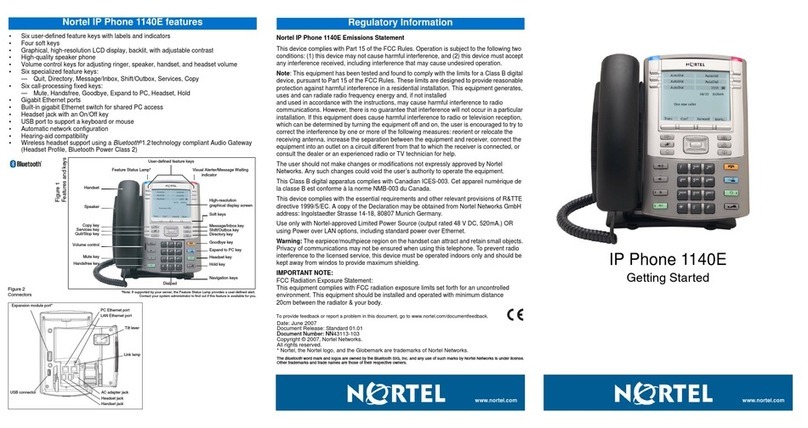
Federal Communications Commission StatementFederal Communications Commission Statement
Part 15: Class A Statement.Part 15: Class A Statement.This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to Part 15 of theThis equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to Part 15 of the
FCC Rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is operated in a commercialFCC Rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is operated in a commercial
environment. This equipment generates, uses, and can radiatenvironment. This equipment generates, uses, and can radiate radio-frequency energy and, if not installed e radio-frequency energy and, if not installed and used in accordance with tand used in accordance with the instructions,he instructions,
could cause harmful interference to radio communications. Operation of this equipment in a residential area is likely to cause could cause harmful interference to radio communications. Operation of this equipment in a residential area is likely to cause harmful interference, inharmful interference, in
which case the user will be required to correct the interference at his own expense.which case the user will be required to correct the interference at his own expense.
Industry Canada (IC) Interference InformationIndustry Canada (IC) Interference Information
This digital apparatus does not exceed the Class A limits for radio noise emissions set out in the radio interference regulations of Industry Canada.This digital apparatus does not exceed the Class A limits for radio noise emissions set out in the radio interference regulations of Industry Canada.
Le Présent Appareil Nomérique n’émet pas de bruits radioélectriques dépassant les limites applicables aux appareils numériques de la class A préscritesLe Présent Appareil Nomérique n’émet pas de bruits radioélectriques dépassant les limites applicables aux appareils numériques de la class A préscrites
dans le reglement sur le brouillage radioélectrique édicté par le Industrie Canada.dans le reglement sur le brouillage radioélectrique édicté par le Industrie Canada.
European Union Declaration of ConformityEuropean Union Declaration of Conformity
The “CE” mark affixed to the equipment means that it conforms to the referenced European Union (EU) Directives listed below:The “CE” mark affixed to the equipment means that it conforms to the referenced European Union (EU) Directives listed below:
EMC EMC Directive Directive 89/336/EEC89/336/EEC
Low-Voltage Low-Voltage Directive Directive 73/23/EEC73/23/EEC
For more information on standards compliance, contact For more information on standards compliance, contact your local distributor.your local distributor.